
5 original techniques to hack an Instagram password
It’s back to school, things are starting to move and on social networks we can feel it.
People are back from their holidays. Whether it is for parents of pupils or students, spouses or friends, it can happen that our curiosity leads us to want to be interested in what the other publishes on their Instagram platform . A curiosity that may well be legitimate in many cases, such as the example of a parent for his children. Nevertheless, in practical terms, curiosity in such a way as to lead to stalking for other people is totally illicit.
This article will also interest you: 4 tips to hack an Instagram account
In our article for purely educational purposes, we will detail some rather original techniques used by some to be able to monitor or collect login credentials on Instagram. One way or another these techniques are generally dedicated to enthusiasts. They range from the simplest technique to the most sophisticated.
1 – PASS DECRYPTOR
This software specially designed to help people who no longer have access to their Instagram account to find it. By entering only your email or username or phone number.
This application uses an algorithm based on the exploitation of so-called “sensitive” databases. From there he will be able to find and display the password of the Instagram account in question.
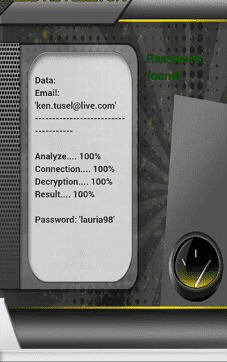
Enjoy this tool now! Finding access to your Instagram account has never been easier…
You can download PASS DECRYPTOR by following this link: https://www.passwordrevelator.net/en/passdecryptor
2 – Social engineering
Social engineering is a proven technique in the cybercrime community. If you recall, last year’s high-profile Twitter attack that led to the account takeover of several celebrities including Elon Musk and Bill Gates, was social engineering.

However, it is a method that does not really require computer expertise. All you need is tact and a good dose of sociability. Indeed, it is possible to extract information from a person who trusts you. Especially if that person might be your child or spouse. You just need to be patient and ask the right questions at the right time regarding these Instagram login methods. Without knowing it, he may be required to provide you with enough information that will allow you to guess his password.
3 – Eavesdropping
It is a technique that allows an interested person to have access to several pieces of information belonging to another person targeted by him. However, it requires certain skills. It simply involves intercepting data via network traffic. It can also be a password or an ID, ideas or even financial information.

Of course, this technique is illegal. Generally, the technique called “eavesdropping” falls into two distinct categories.
On the one hand we have passive listening and on the other active listening:
– Passive eavesdropping: to do this, it is simply necessary to intercept data resulting from the targeted person’s network traffic. Typically these are communications such as a text or video message.
– Active eavesdropping: this will consist in usurping the identity of a terminal close to that used by the targeted person. In this way, you can send requests to the transmitters of your target. In relation to the answer, it will therefore be easy for you to collect the passwords that interest you.
Unfortunately, this is a technique that is heavily embarrassed by end-to-end encryption. If the person and uses an encrypted network, it will therefore be impossible to do so.
4 – Cross-site Scripting
In this case, we can indeed use this technique to collect information. Indeed, it will suffice to insert a JavaScript-type script into the database of a particular website.

A site that can be visited regularly by the targeted person. When the Internet user’s browser connected to the site executes the script sent, it will then be possible to hijack the latter’s session, thus allowing several actions to be carried out such as what interests us, the collection of personal information including passwords past.
5 – The LED Blink Attack
When an electronic device with a screen is used, this device emits LED flashes at each session and at each action. Imagine that these LED light flashes can delay collecting personal information. Indeed, it has been proven by Israeli researchers from the Ben Gurion University of the Negev, how to use connected speakers or even computer speakers, combined an observation of small LED lights that most often flash on devices electronics that we use on a daily basis such as computers or smartphones, it is possible to hack a person.

This would require an electro-optical sensor that would simply be connected to a standard telescope. In this way, with each flicker of LED light, the change in voltage can be converted into an electrical signal. Signal thanks to which we can exfiltrate a soundtrack that would be sufficiently intelligible to know the information contained during the session by the target. It must be pointed out that the flickers in question here are invisible to the naked eye.
According to the researchers who discovered the technique, it can be performed on 50% of the devices we use every day. Like what the Israelis have not only invented Pegasus, but in addition, very sophisticated techniques.
Now access an unlimited number of passwords!