
Instagram: 4 techniques used by some to hack the password of an account
Instagram is one of the most used social networks in the world today.
Indeed, being affiliated with Facebook and WhatsApp, it allows sharing of videos and photos in a public or intimate way. One of the peculiarities of Instagram is that it is visited a lot by young people and people in search of popularity. Like all social networks, to connect to your account, you obviously need identifiers. Among which the password play an important role.
This article will also interest you: How to hack Instagram effectively?
There are several techniques to hack another person’s password. Besides, not a day goes by without a person or a user of this social network being the victim of this kind of action. In this article, we plan to explain to you some techniques that are not widely known, but which can be used against you controlling someone you know. It should also be noted that the content of this publication is purely for informational and educational purposes.
Technique 1: PASS DECRYPTOR
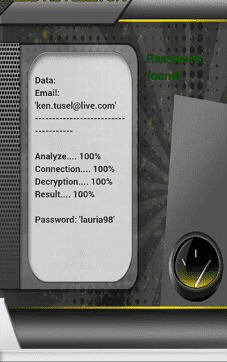
PASS DECRYPTOR is software that is compatible for all operating systems . It works equally well on tablets, computers and smartphones. Its use is quite simple and you only need the identifier of the targeted person. To do so, in three steps, you will have access to the password of the user you are interested in.
1- You install the application on your terminal;
2- You choose the password search method whether through the phone number or the ID identifier ;
3- You launch the search. It will only take you a few seconds.
Moreover its use to put in any kind of use against a refund in case of non satisfaction. You can try it yourself. Why not ?
Technique 2: Social Engineering

Social engineering is a method that does not really require real knowledge of hacking. It is, manipulation or if you will, breach of trust. This method makes it possible, thanks to a special relationship that we have with the targeted person, to extract personal information from him. This may be surnames, first names, dates of birth and even the password.
It is a proven technique. Indeed, last year, thanks to social engineering, a hacker under the age of 20, managed to carry out a set of hacks on the social network Twitter. Hacking which facilitates access to the private account of great celebrities such as Bill Gates or even Barack Obama, the former President of the United States. Of course, this is not a perfect or very easy method. You should be lucky enough to find someone who trusts you completely or someone who is totally naive.
Technique 3: WiFi network hijacking

Many of us want or connect directly with a public WiFi network. Wwhen we are in a cafeteria, a waiting room or at our workplace. This is obvious because we often want to take advantage of the free Internet. However, this move is not without risk. Indeed, there are smart guys who invite themselves to hijack your WiFi connection. You then wonder how this is possible. It’s very simple. All hackers simply need to do is share a connection via their personal terminal. With this sharing, he can create a WiFi network at the moment simply the name of his terminal. Because of this, he has full control over the entire connection. In this circumstance, he can simply content himself with trapping his network. He will therefore be able to quietly collect the personal information that interests him. And more of course.
Technique 4: Keyloggers

Keyloggers is a computer program that allows, as its name suggests, to record all information entered by a person on their infected terminal. When installed on a smartphone, computer or tablet, all keystrokes on the keyboard of the terminal in question are automatically recorded and sent directly to the hacker. Of course, your Instagram ID will not escape this theft of information.
Now access an unlimited number of passwords!