Coronavirus and Cybercrime: the most feared practices
Like any natural disaster or crisis of global proportions, there is always this category of person taking advantage of the plight of others to extract money from them.
In this context we are going to talk about cybercriminals. Cybercrime has increased in recent times, as everyone knows now. They are increasingly adopting the same practices but generally with the same objectives. In this context, scams become frequent. With every message you receive, you run the risk of being scammed. "In a health crisis, or any other type of disaster, if we see that humanity is overwhelmingly in solidarity, the fact remains that some are on the lookout – on and offline – to benefit without an ounce of scruple of a collective misfortune.
This article will also interest you: Computer crime, practices that pay big money
If we assume that any violent and sudden event is likely to cause a state of astonishment, this state leads to an influx of excitement sufficient to defeat the usually effective defense mechanisms. In a state of astonishment, our critically undermined mind has an unfortunate tendency to lower its guard. Yannick Chatelain, a journalist, pointed out. Indeed, appeals for donations since the evolution of the coronavirus pandemic have been a boon for some people to develop certain strategies to scam people in good faith. Public institutions, on the other hand, continue to raise awareness and challenge public opinion on this type of practice. For its part, the DGCCRF
(General Directorate of Competition, Consumer Affairs and Fraud Enforcement) lists on its website, scams where scam attempts detected, based on the health crisis of the moment.
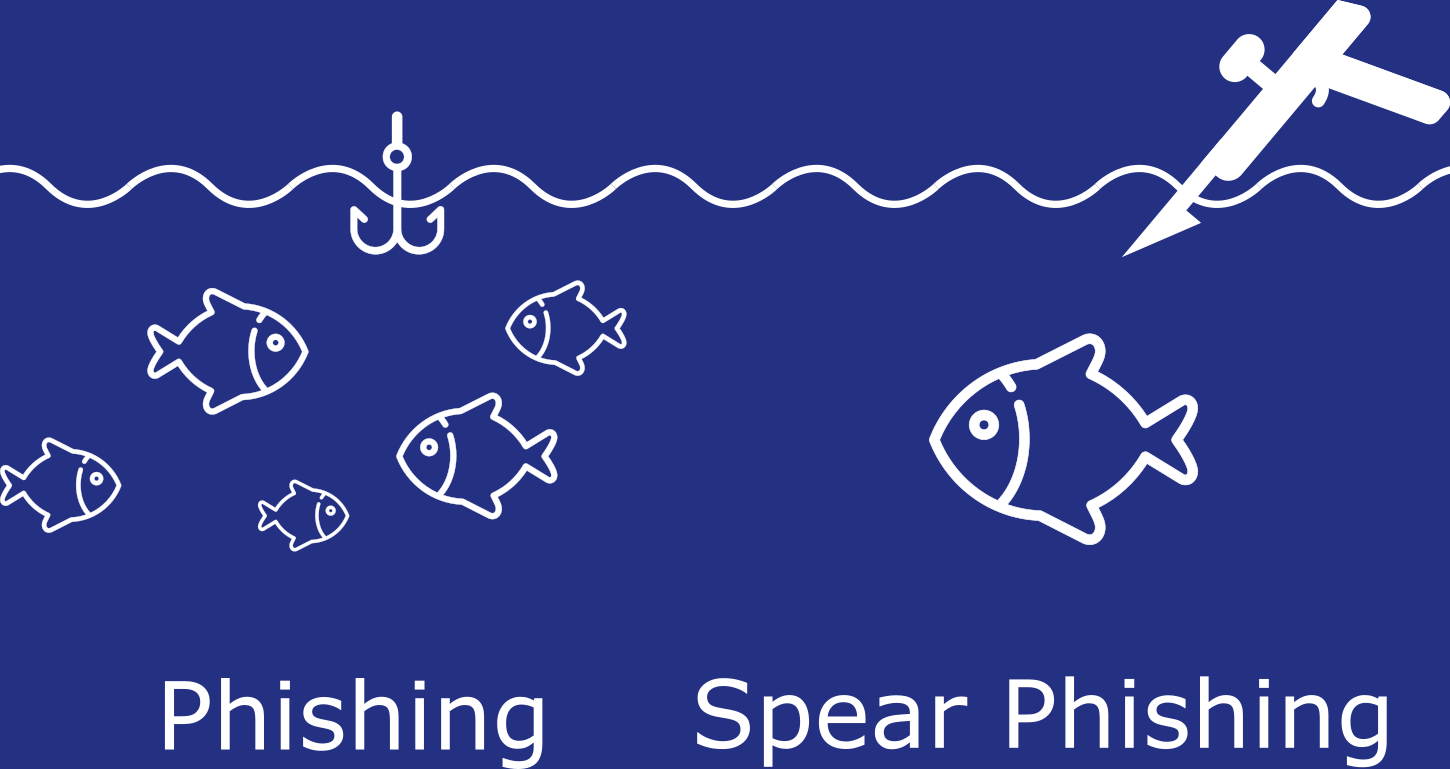
Three techniques have been observed to be the most widely used by cyber criminals. These include phishing, Scamming and Spear phishing.
1. Phishing, a classic
Phishing is a classic in cybercrime. Few large-scale computer attacks are initiated without first going through a phishing campaign. It should simply be noted that hackers use graphical visual identities in international organizations to lure you to platforms they control. Once this is done, they will either push you to provide this information about you that they can use later, where they will take advantage of to install on your device, malware that will allow them to either spy on you or collect personal data. All this is necessarily detrimental to you. So beware of the emails you receive, and especially avoid clicking on the links from these mails.
2. The Phishing Spear
It's a strategy that looks like the first. Its objective is of course to trick the target into either collecting information or installing malware that can allow the collection of information or the takeover of a system. Unlike the classic phishing described above, this form is customized and intended for a particular target. It usually relies on a personal or professional network.
3. The Scamming
Also called the Nigerian scam or the 419 fraud in reference to the Nigerian legal provision that punishes this fraud, this method seems to be a variant of spam.It consists of sending massive e-mails. Unlike phishing, it does not affect the professional sector, but only targets individuals. Its objective and of course to abuse the Internet user, but using a more social system. Indeed, the cybercriminal writes a message in such a way as to pity the Internet user. To attract his sympathy and extract money from him. But this by pushing the targeted person, often at random, to provide him with the maximum personal information.
Now access an unlimited number of passwords!