
10 practices for safe telecommuting
As the saying is, you are never over-prepared.
Indeed, at a time when telework is widespread, it is clear that good practices must be developed while making trade much safer. That's why in this article, we'll give you tips on how to secure your exchanges while telecommuting.
1. Have a terminal protection program

The first piece of advice is basic. Simply install software on your smartphone or your smartphone or your tablet used as part of telework to protect it. There is no shortage of offers in the antivirus market. But in the current context, any antivirus will not do. In fact, you will need to obtain software that can adapt and learn. Software that supports machine learning. Software that will be able to protect you from data exfiltrations or ransom programs
2. Prioritizing mobile devices

Mobile devices are most often overlooked in this case the smartphone. Yet these small devices are increasingly becoming the royal route of cybercriminals. If the average user does not see the reference, it is clear that sooner or later, the computer tool will be used work but also for personal things where one is not necessarily attention to security.
3. Update the settings of the home internet box

These devices are usually provided with default settings. This means that credentials such as passwords need to be changed. But who says changed the password does not mean that one should afford to use a password that is easy to draw. It must be both complex to guess but as simple for you to remember.
4. Apply security updates to all your devices

Updates are essential. They help fill vulnerabilities previously discovered by computer security specialists. But these security vulnerabilities are often also discovered by hackers who want to use this to their advantage. That's why you should never look at any program's security update. Practice has clearly shown that the lack of implementation of updates to cause much more damage
5. Protect online meetings with passwords
Since the beginning of mass telework, it has been revealed on several levels of intrusions at meetings often myself confidential. Unfortunately it has been observed that many professionals do not protect their meeting on video conferencing apps such as Zoom.
6. Beware of unknown matches

90% of software attacks were based on successful phishing attacks. This is why you are asked never to click on messages when you do not know the recipients or when the recipients present a certain risk at the same minimal. This is where phishing attacks usually come from.
7. Check your network by scanning it

Today, there are several tools to scan your Internet network. This allows you to lay bare parasitic programs to endanger your devices but also your data.
8. Connect with a VPN

Private virtual networks add a layer of security to the connection by improving the confidentiality of exchanges. This is very important in a context where sensitive and confidential data will have to be exchanged.
9. Embrace multi-factor authentication when identifying
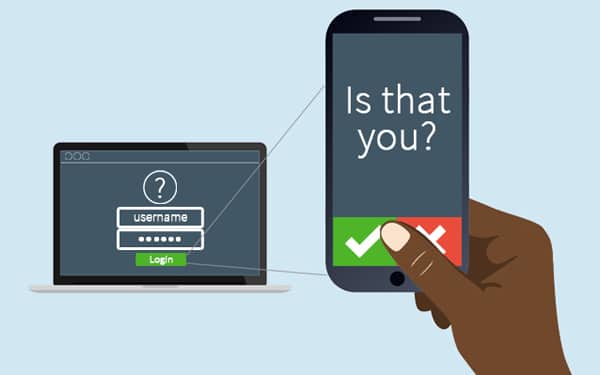
Additional security measure. This measure will minimize attempts to desire passion for identity. This will prevent a person from a non-service or level from accessing information that he or she should not in principle.
10. Always check privacy settings

Before validating an application or computer tool, you must ensure that the permissions required by these tools are not likely to violate the privacy of your data. Giving too much permission can in some way harm your computer security.
Now access an unlimited number of passwords!