Cyberattacks 2020: More and more victims
The number of victims of computer attacks continues to grow.
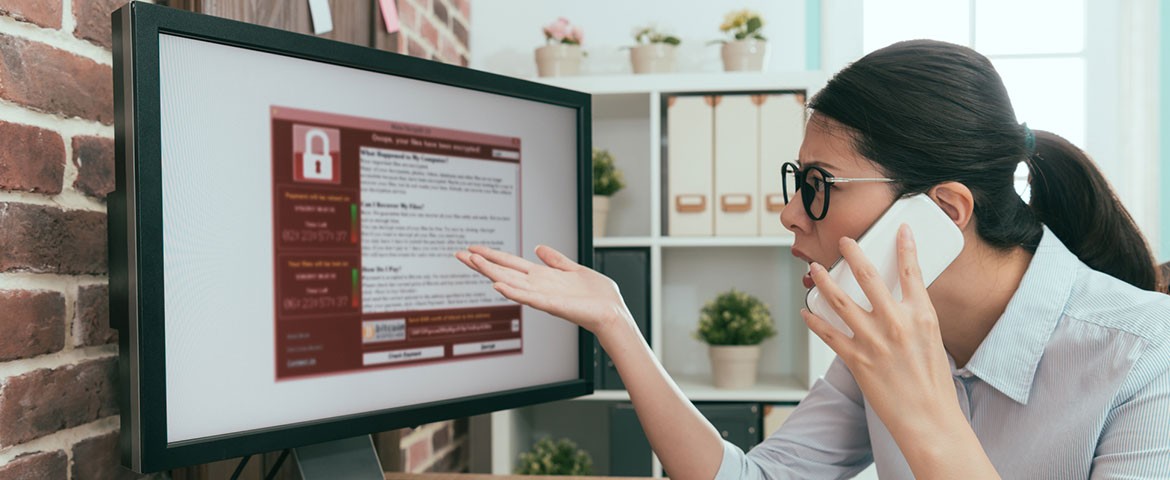
Since the beginning of the year, the IT sector has not stopped being alerted and tossed around. With the coronavirus pandemic, cybercriminals have moved up a gear. Ransom demands have multiplied. Attacks have become much more relevant than before. If 2019 had been designated as the year of ransomware, it is clear that 2020 with everything that is happening has clearly dethroned it. According to the National Information System Security Agency, there is an "unprecedented increase" in the use of ransomware.
This article will also interest you: The year 2020 already has twice as many attacks as 2019 according to ANSSI
In his exchange with the senate, Guillaume Poupard, the head of the National Agency for Security of Information Systems, noted that ransomware attacks in 2020 in France are multiplying by "three or four". "This is particularly worrying," he noted. According to the latter, there is nothing to suggest that this problem decreases in intensity in the short term. Indeed, on closer look, we see that the number of companies affected by cyberattacks continues to skyrocket. Every week a new victim is reported.
Victims include not only large companies, such as the defence-affiliated Sopra Steria company, as a digital solution provider (having lost nearly 40 to 50 million euros as a result of a ransomware attack) or the territorial community such as the towns of Alfortville, Vincennes or the community of Marseille. Small businesses are not on the margins of this explosion of cyber malice.
According to the government's cyber-protection prevention platform, nearly 1,328 victims have been identified.

The modus operandi of cyberattackers is purely a classic. Most of these cyber-evil acts began with the sending of a corrupt email. An email that contains good on an attachment. "We are no longer in the caricature of the mistranslated email with faults, it is now sophisticated enough that a person who does not have the automatisms is fooled," means, Brice Augras, ethical hacker, boss of a Brussels consulting firm BZHunt. With the opening created by the attachment, hackers will then be able to break into the targeted company's computer system. "Opening the attachment will allow attackers to get into the company's IT. Cybercriminals, after remotely circising computers, encrypt Excel files, PDF or Word documents, and then demand a ransom in cryptocurrency. The sums requested range from a few thousand euros to half a million euros, a sum requested this year from a Breton company," explains Brice Augras.
At this level, it has been observed that attacks on ransom programs are becoming too profitable for its malicious operators. This is likely to encourage them to do more and to be more demanding.
"The first ransom demands that indiscriminately targeted Internet users a few years ago were followed by more targeted attacks on companies, sometimes with ransom demands adjusted for corporate revenue. While the identity of the criminals behind these software is not known for certain, the activities of computer scientists in Eastern Europe are closely watched. Sometimes rightly so. Explains the ethical hacker. An example to explain this situation, we have the trial that took place in mid-October, which is quite rare of its kind, but which mid-naked the case of Alexander Vinnik who had been suspected, of having been involved in the actions of Locky ransom software. The judge's decision has not yet been rendered and apparently will not be long.
The situation continues to get worse. Some security experts are beginning to fear for 2021. Organizations need to be prepared to approach the new year with a lot of complexity and strategy. Because that's what cybercriminals will do. According to several studies, whether at the level of ransom software, social engineering and vulnerabilities affecting devices related to the Internet of Things, there will be some evolution of cyber malice.
Now access an unlimited number of passwords!