
Cybersecurity and health care: Government adopts appropriate measures to close security gap
Since the beginning of this year, the French government has expressed its desire to improve the computer security of health facilities that are increasingly targeted and affected by the wave of cybercrime in the digital sector.
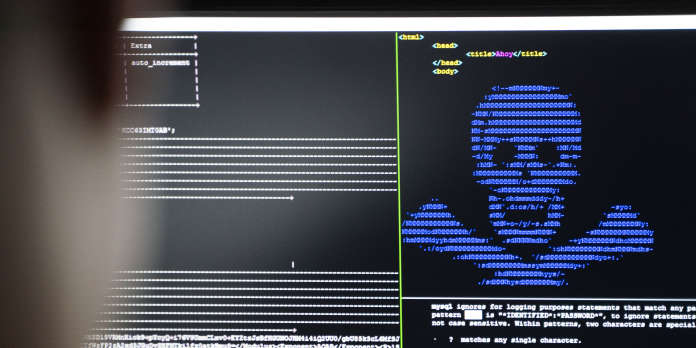
During 2020 and early 2021, dozens of hospitals and analytical laboratories were targeted by more or less sophisticated cyberattacks, usually based on ransomware.
The government's objective is to make it a priority to defend the computer systems of these institutions. For this several proposals and projects have been developed. For this reason, the public agency responsible for defence in the field of computer security, the independent administrative authority that is the national computer security agency decides to deploy the major means. The goal? "Raising the level of information system security thro[…]ugh the implementation of security pathways tailored to the issues and needs of organizations," the administrative authority explains on its website.
As a reminder, it should be said that a long time ago, the authorities were asked that the computer systems of health facilities were particularly vulnerable. The National Information Systems Security Agency itself has repeatedly painted a picture of this aspect. Especially by highlighting the "most immediate threa[…]t in terms of volume, frequency of attacks and consequences" that is ransomware.
This very important aspect is of the priority on the French government. He also announced the release of several budget measures to this effect. "The National Cyber Security Strategy has allocated ANSSI a budget envelope of 136 million euros to strengthen the state's cybersecurity. Of this amount, 2[…]5 million euros will be dedicated specifically to securing health facilities," explained Health Minister Olivier Veran and Secretary of State for Digital Affairs Cédric O.
We find that the words are followed by the acts months after.
"The support of beneficiaries is the key word in this service offering through the implementation of security paths tailored to the challenges and needs of organizations," says the National Information Systems Security Agency. Unfortunately, these clarifications for institutions cannot be a beneficiary of this program. In order to be able to solicit the agency's expertise, certain conditions would have to be met: "All beneficiaries must have an existing information system;
Each candidate organisation must be supported by its decision-maker, who holds legal and administrative responsibility, in order to ensure the full involvement of the teams and the smooth running of the actions carried out," stresses the administrative authority.
By these criteria we can detail 4 computer security circuits. Which starts with the foundation course and ends with the reinforced course. "The point of passage for organizations operating a service of a level comparable to that of an essential or vital information system. Once the action plan is selected, it is a matter of implementing the route. ». The circuit is divided into three stages:
"Step 1, launch: implementation of the initial pack." A so-called "field" provider provides awareness, training and auditing to the recipient. Together, they develop a security plan listing concrete measures to be implemented. Explains the information systems security agency on its website.
The second step is essentially based on deepening. We're talking about the implementation of relay packs. "The process continues with the implementation of the security plan measures. New projects can be launched as the recipient's level of cybersecurity changes. ».
As for the last step, we will talk about iterative follow-up. Indeed, it will be ensured that the claimant who is supposed to accompany the beneficiary of the program must guide the beneficiary to validate his objectives.
With its first steps initiated by the French government, it is hoped that some improvement in the security framework for health care in the face of the rise of cyber-malian operators who are always as quick to act.
Now access an unlimited number of passwords!