
How to hack Snapchat account? Here are 3 commonly used tricks
If you have a Snapchat account and want to know if it is protected enough to prevent cybercriminals from stealing it from you, in this article we have offered you some tricks which are commonly used to determine the Snapchat account.
Learning its methods can be useful not only to protect yourself, but also to recover your account if you have already been a victim of this. We would like to clarify that the content of this article is purely educational. We therefore advise against using it in contexts that could violate the law.
This article will also interest you: How to hack Snapchat effectively?
1 – Use PASS DECODER
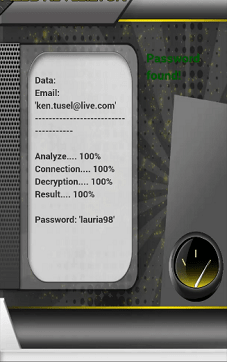
PASS DECODER is a computer software that gives the opportunity to its user to find any Snapchat account password. It was designed to be used by anyone even if you don’t have advanced hacking or computer skills. With the power of its algorithms, this software will help you at the same time to find the passwords you need without worrying. To do this, you will have to follow three very simple steps:
– First of all, you have to download and install the software on your terminal. It should be mentioned that it is a computer program that can be used from a Windows computer, a smartphone whether Android or iOS and a digital tablet;
– Next, choose the password search method. You can find the password for a Snapchat account using either the phone number associated with the account or the email address;
– Finally, you launch the search and you let the software find the necessary connection identifiers.
In addition, the software is guaranteed for one month of use. You are satisfied or refunded.
2 – Social engineering

This is a practice that is not really hacking. Yet it is widely used by cybercriminals to collect important information. For example, if you see a post that asks you for the name of the school you attended in elementary school, that is clearly suspicious, although such posts are often harbored for amusement or distraction. Social engineering will consist for the cybercriminal to weave a link between you. Gradually, the latter uses this link to collect personal information that it will convert into a connection identifier. Therefore it is much more manipulation and breach of trust.
3 – Online databases

There are today on several online platforms, databases that contain a lot of personal data and login credentials. Its databases most often come from data leaks recorded by our various platforms and social networks. They can also consist of information collected during computer hacking or of an aspiration of data published by the users that even in the access is public. With its databases and a mastery of analytics, cybercriminals can find login credentials. Today, it is possible to find this information on several platforms, in particular on the Dark Web, where it is often made available free of charge with payment.
Now access an unlimited number of passwords!