
3 tips to hack Instagram
Along with WhatsApp, Instagram is one of the applications that are included in the Facebook group.
These three computer programs constitute the largest and most widely used social networking platform in the world. The fact that they are the most adored by digital users because of their functionalities and the advantages they can offer us, these social networks are part of our daily lives. Therefore, it is not uncommon for individuals to be interested in getting done.
This article will also interest you: 5 original techniques to hack an Instagram password
Hacking an Instagram password can have several interests in relation to the situation of those who wish to hack, for example. In a way, there are parents who want to know what their children are doing on this social network which is adored by young people, among other things. There are also spouses who want to monitor their companions. And hackers to impersonate identities to carry out phishing and online scam campaigns . To achieve its more or less illegal objectives, they will use different methods that often work and others do not.
In our article, we aim to explain to you some techniques that are generally used by hackers or individuals in order to gain access to an Instagram account. Our goal is to make you understand the very risk behind account hacking, but also to train you to the extent that you are interested in an educational understanding of the subject. However, we absolutely want to warn you of the illegal nature of computer initiation.
If you are not a member of law enforcement, you have no right to use these techniques in order to access the account of someone who does not give you legal authorization. However, it is possible to often be able to put these lessons into practice to help loved ones recover their accounts in the event of loss.
Technique 1: Use PASS DECRYPTOR software
PASS DECRYPTOR is software that can be used on a smartphone, tablet or computer. It is compatible with Android, Windows and iOS. Its use is very simple. You just need to download the application on your dedicated terminal, to choose the method allowing you to find the password of the account concerned. Let’s talk about it, it must be meant that this program gives the advantage to its user to have the password of the targeted Instagram account.
Moreover, there is no need to install it on the target device. Unlike many applications that will be presented, this one only installs on your device. Then you need to know either the email address associated with the Instagram account or the phone number. Of course, this is information that is easy to discover. Then you simply launch the search which will only take a few seconds.
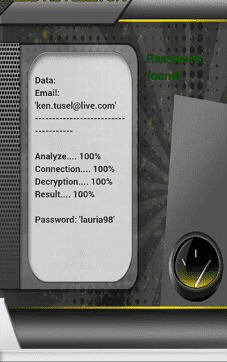
This software offers the advantage of being satisfactory or the user will be reimbursed. As we speak to you, thousands of people have already used it.
Technique 2: Use a keylogger
The keylogger and software that allows its user to be able to copy everything that an individual enters using his keyboard. In other words, if you enter your login credentials for example no matter what account, the operator behind the keylogger to get them. Indeed this software is quite scary.

However, it is necessary to highlight something quite complicated in its use. Unlike PASS DECRYPTOR, WHICH DOES NOT REQUIRE an external installation, i.e. on the victim’s terminal, keylogger by its nature requires that it be installed on the computer, smartphone or tablet of the person you are targeting. And of course it’s not a simple enough task, especially when you don’t have a good knowledge of hacking itself.
Technique 3: Steal the password saved in the browser
Unfortunately, many users have this habit of saving their passwords when they connect to browsers. Which generally tends to expose them. It is just enough that the person who wants to hack is able to access the browser. Go to the settings and retrieve the login credentials already saved.
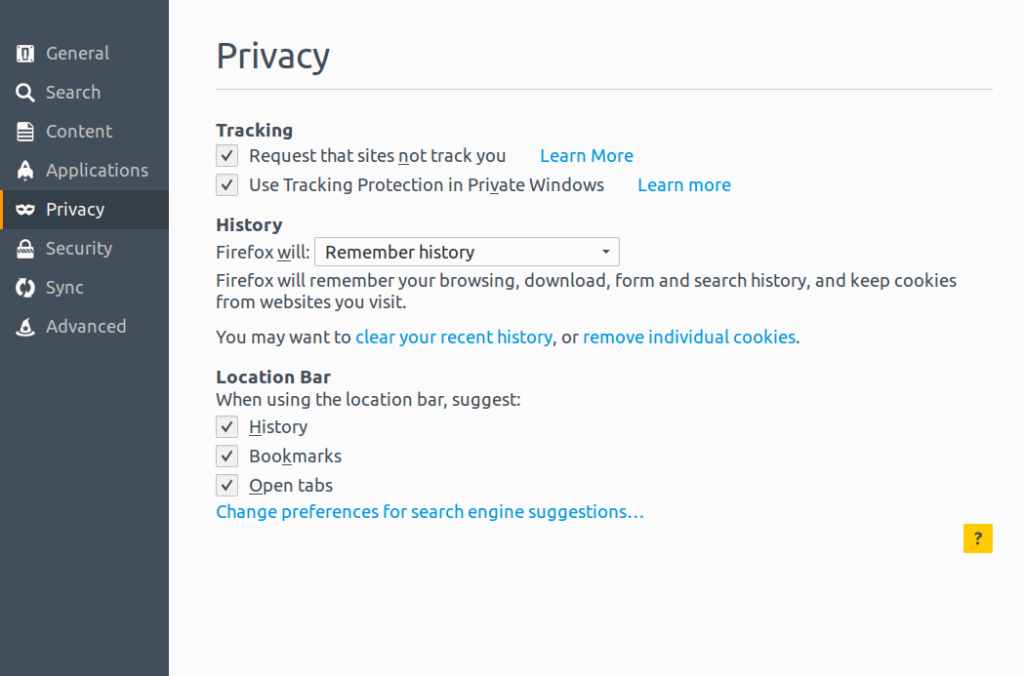
A very simple and effective technique. However, it is a technique that is difficult to achieve remotely. In other words, when you don’t have the terminal at hand and the browser easily accessible, you should then consider a type of remote hacking such as Hijacking for example. This is what will obviously require a good command of hacking and session and cookie hijacking. I leave you to imagine the hassle that this imposes. But if you’re a savvy hacker, that certainly won’t be a problem.
Now access an unlimited number of passwords!