
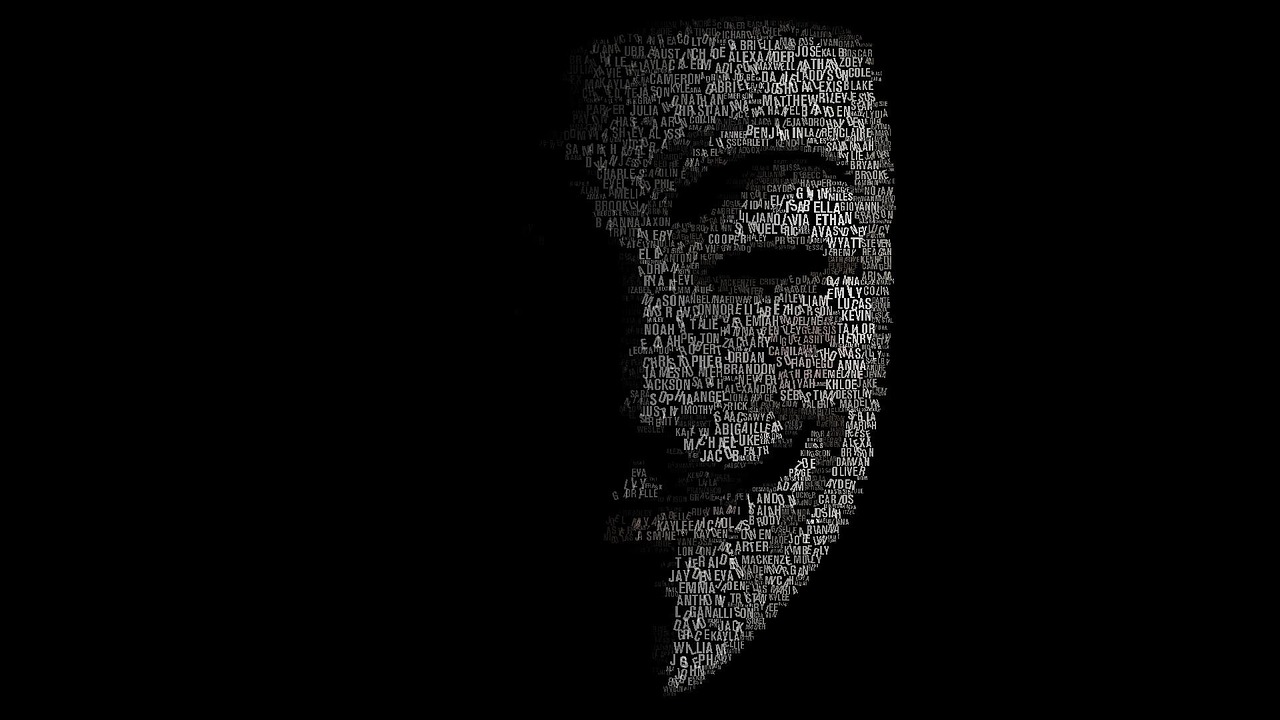
Black Hat vs White Hat Hacker
Not a week goes by without us learning that a new hack of personal data has taken place. Whether it's recovering email addresses, hacking Facebook, stealing a Twitter password or hacking a wifi, hackers are spoilt for choice: websites are still rarely 100% secure.
Yet in the hacker world, it is important to distinguish the Black Hat Hacker from the White Hat hacker:
The Black Hat Hacker: Malicious Hacking of Computer Data

The black hat hacker's goal is simple: to steal personal information from websites for the purpose of disseminating it. In general, the hacker puts pressure on the website from which the data originates in order to obtain a financial consideration (in order to avoid the dissemination of the data). However, the consideration requested is not always financial.
Take the example of the AshleyMadison website, which specializes in extramarital dating. In July 2015, hackers hacked data from the dating site's accounts receivable. The case caused a lot of noise as the hackers demanded the closure of the website. Otherwise, customer information would be posted online. A threat that has not been taken seriously enough: the personal data of customers was leaked on the web in August 2015!
The White Hat Hacker: A Professional in the Service of Data Security
Data hacking is not always malicious. Indeed, there are so-called White Hat Hackers: here the goal is not to disclose the information on the web. Rather, the goal is to identify a security flaw in order to encourage websites to find a safer solution for the personal data of Internet users. Some IT security companies specialize in this niche and work with the world's largest companies and organizations. But sometimes the White Hat Hacker is not part of a cybersecurity company: it can also be an individual (or a group of individuals).
At the end of 2013, the social network Snapchat was massively hacked. The hacker's goal was not to disclose users' personal information, but rather to warn them that social networks are not taking all measures to protect their data. It was also a demonstration urging Snapchat to better secure its social network.
A very thin border between Black and White Hat?
The line between the hacker Black and White Hat is thin. Indeed, hackers who break laws to prevent security breaches are considered to be cyber-terrorists (black-hat), while they call themselves White Hats. The name White Hat is currently reserved for cyber security professionals.
Now access an unlimited number of passwords!