Understanding cyberattacks and malware
According to a statistic compiled anonymously based on several requests from the Threat Intelligence portal of the Russian cyber defence company Kaspersky, about 72%, or three-quarters of the malicious files that have been analyzed in recent times, categorizes itself into three particular areas of cyber malice:
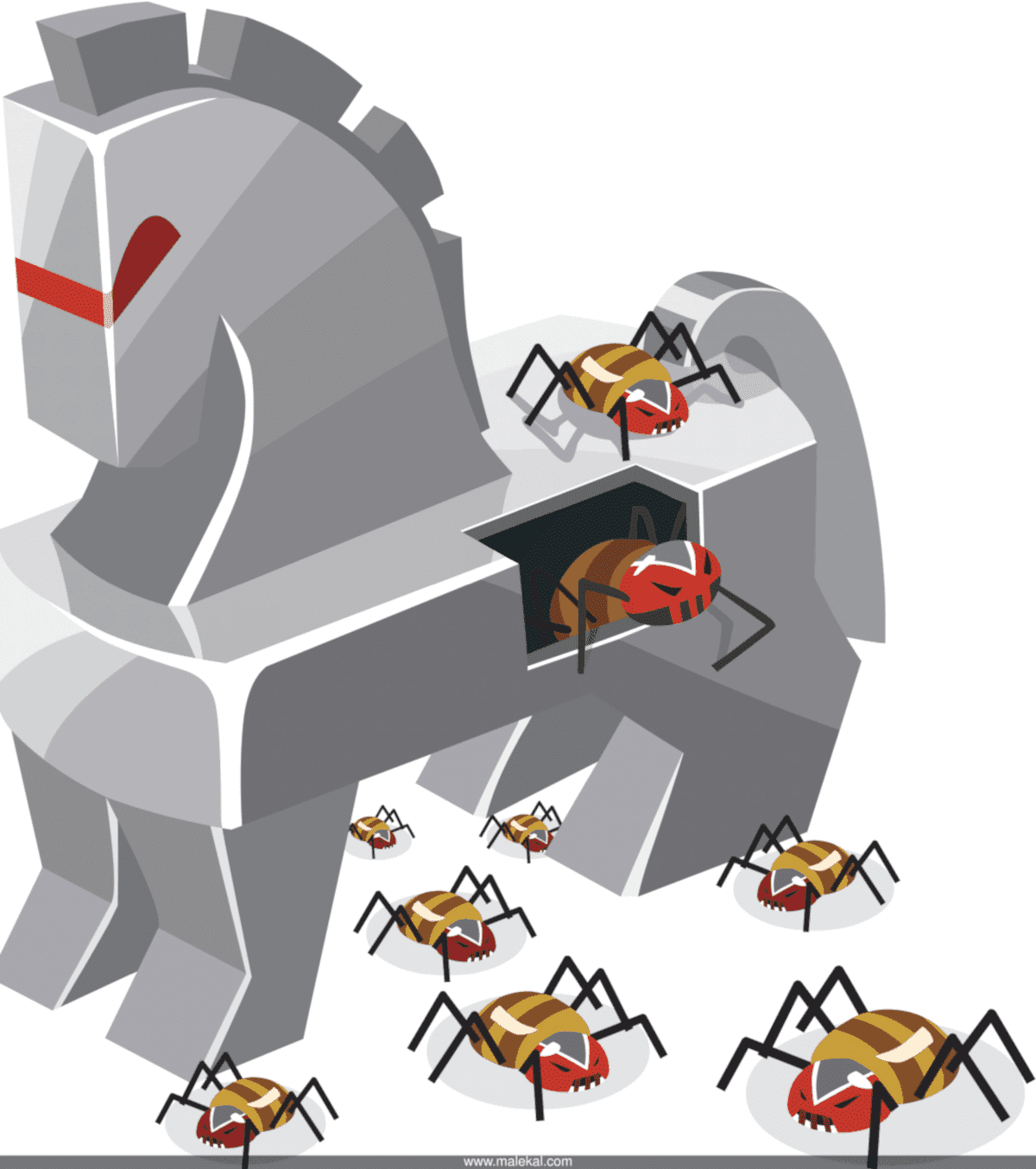
– Trojans (Trojan)
– Backdoors or backdoors
– Malware injectors (Dropper)
Thanks to these statistics, it has also been shown that the malware that computer security specialists tend to spend more time on are the most prevalent.
As we know, the starting point of an investigation into a cyberattack and of course the detection of activity deemed malicious. To be able to deploy the necessary measures to address the problems posed by a computer incident, cybersecurity specialists must be able to:
– Identify the target targeted by the attack
– The origin of a malicious program
– The popularity of this program
This allows analysts to react effectively. Kaspersky's portal on computer threats is available to cybersecurity professionals, especially in the analysis of computer incidents. As a result, several requests are made to Russian society on a daily basis in order to obtain assistance on security issues. Regularly carrying on malicious objects, in the treatment seems a little trickier.
In the majority of cases, the most proposed or expertly reviewed incidents on:
– 24% of the backdoors
– Trojans in 25% of cases
– Malware players for 23 percent of requests
These malwares are usually used by their publishers to take control of either their target's computers remotely as is the case with Trojans and backdoors, or to be able to install pirated objects without the latter's knowledge, pirated objects in the case of Droppers.
In addition, Trojans generally perceived by many studies as the most common malware in the world. It is a category widely used and appreciated by cyber criminals. Probably because of the features they offer them. The backdoor and malicious file injectors are relatively unknown, and therefore less common. They make up only 3% of the malicious files usually blocked by the antivirus provided by Kaspersky.
One can understand on the result by referring to the fact that generally specialists tend to be interested in the final target of a computer attack. While in a majority of cases, terminal protection software tends to block them as quickly as possible. For example, it is known that the security product in a concrete way prevents the user from opening corrupted emails, which usually prevents certain malware from being able to achieve their ends. As for program injectors, they are only recognized when researchers are able to identify all the components that make up it, which is not a task but to be carried out.
In addition, the popularity of a malware also depends on the general interest in computer incidents in which it has played an important role and the requirement that researchers often analyze them in more detail. Take, for example, the case of the Emotet malware, which follows several press articles to pique the interest of cybersecurity researchers. On the other hand, following several security flaws involving Linux and Android distributions, the backdoors have been screened several times by specialists in order to better apprehend them. And this is the case for several vulnerabilities affecting Microsoft Windows.
"We noted that the number of requests sent to the Kaspersky Threat Intelligence Portal to verify viruses or code elements that fit into other programs is extremely low, less than 1%. However, it is traditionally one of the most common threats detected by incident protection, detection and response (EDR) solutions. This type of threat replicates and deploys its code in other files, which can lead to the appearance of a large number of malicious files in the infected system. As we have seen, viruses are rarely of interest to researchers, probably because they lack originality compared to other threats," says Denis Parinov, acting director of heuristic detection and threat monitoring at the Russian cybersecurity firm.
Now access an unlimited number of passwords!