Webex: Cisco works to close security flaws in its app
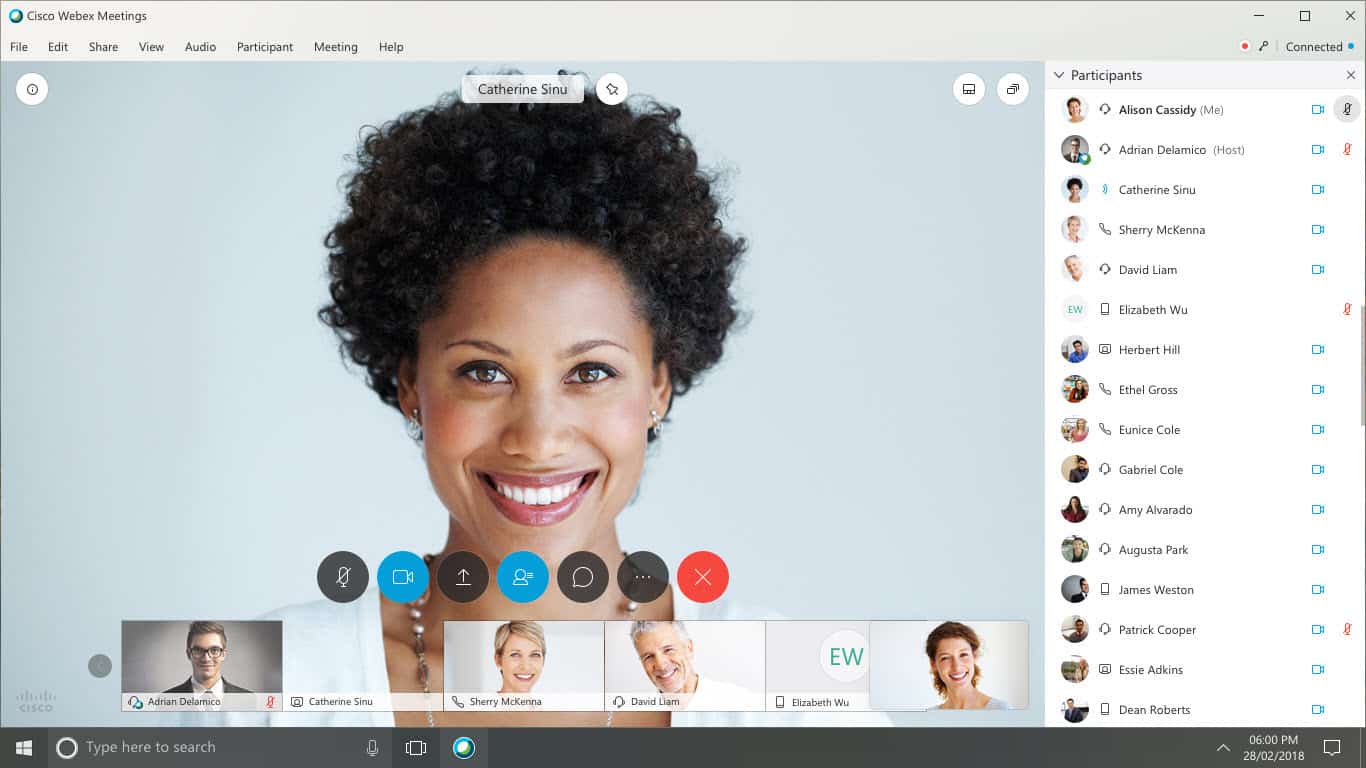
Webex is one of its remote collaboration applications, like Zoom or Teams, which has been hugely successful since the first containment in March and May 2020.
According to an expert in the evaluation of the experiment, Aternity, the use of the Cisco platform, saw an increase of 451% in just 2020.
Recently security vulnerabilities had been discovered on Cisco's teleconferencing applications, Webex. These vulnerabilities could allow people to infiltrate relationships as ghost people so as to be invisible to other participants.
This article will also interest you: Videoconferencing: how to determine the most secure applications
The security flaws were discovered by IBM researchers in a study of several remote work tools most used by employees during the coronavirus health crisis.
According to the latter, if these vulnerabilities are used in combination and effectively, people could then obtain content that is both video and audio, screen sharing and chat at meetings held by remote collaborators. As a result, they could gather a number of information about the participants in this meeting, such as names, email addresses of IP addresses, and all this while being totally invisible to other participants. This will require the exclusion of other participants.
It was during the famous handshake process, which is usually held at the launch of each meeting through the ex web application, that the IBM researcher was able to detect security vulnerabilities. An automated procedure that allows communication parameters to be established between two different entities before each communication begins.It is as the name suggests a process of linking as it is referred to in English.
Hackers who could obtain the URL of meetings, can use it following several events to access the web server and be able to infiltrate meetings and then steal participants' data during the famous linking.
"We have identified the specific values of customer information that could be manipulated during the handshake process, to make the attacker invisible on the panel of participants," the IBM research team said in its report.
But it is possible for participants to realize that they are being observed by invisible actors. To do this, they should pay attention to an audible signal that often felt during a new audio connection. However, at some meetings that please many people, the host tends to disable the audio signal in and out. This facilitates the then intrusion of the hacker. Moreover, even in the presence of tone, often hearing them neglect the beep that can often be unaffiliating to any participant.
What might seem reassuring is that in order for the cybercriminal to take advantage of security vulnerabilities, he would need to know exactly the unique URL used for meetings through WebEx. This clearly narrows the scope of possibilities.
Currently, Cisco is working with IBM to provide security patches in the coming days.
Now access an unlimited number of passwords!