Hack a Snapchat password
Snapchat account hacking techniques

Hack a Snapchat password
Snapchat account hacking techniques

Do you know a solution to hack Snapchat password? Are you curious about how to get Snapchat account password? Have you been the victim of a Snapchat account password hack?
If your concern is among the questions we have asked above, you have certainly come to the right place.
Since Snapchat is one of the most visited social networks in the world, hackers are very interested in it. Therefore you must learn the techniques to be able to protect yourself effectively.
In this article we are going to give you some of the most effective techniques regarding Snapchat account hacking.
It is important to specify that the content of this article is purely written for educational purposes. Therefore, we strongly advise against using it for any illegal purpose. It should be mentioned that computer hacking is punishable by law and that we in no way encourage any unlawful act.
First you simply have to remember that thousands of accounts are hacked every day. The goal of hackers is to steal personal data or simply steal your identity. They use several methods for this, there are methods that call for the use of specific software, there are also methods that require simple or complex technical manipulations of scripts and devices that we use daily to access the internet and Snapchat. These elements can have their uses that we will describe to you much more towards the end of this article.
Once this point is cleared up, here are the latest password hacking techniques for you:
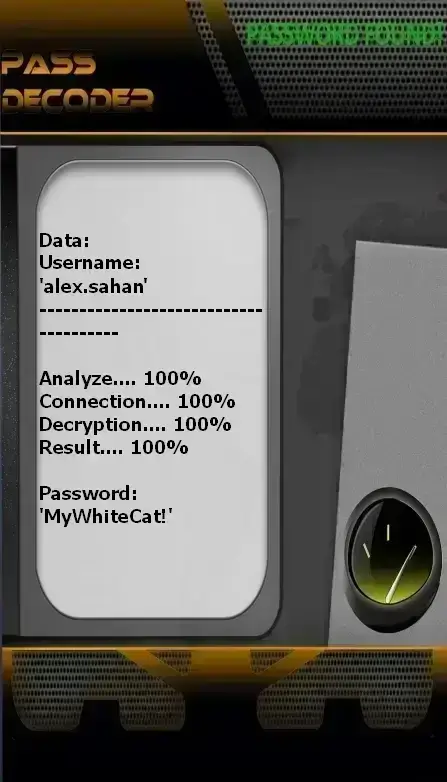
with PASS DECODER
It is an AI-powered application developed to hack the password of any Snapchat account—regardless of which account it is. This application was designed by cybersecurity experts and features a powerful algorithm that reliably retrieves passwords in just a few minutes. To use it, simply follow three easy steps.
The first step is to download and install the application on your device from the official website: https://www.passwordrevelator.net/en/passdecoder
The second step involves providing one piece of information about the account you wish to access. The application requires either the @username, the phone number linked to the account, or the associated email address. In practice, these are easy-to-remember details that you can typically find by viewing the target user’s profile.
The third step is the actual recovery: once you’ve entered the required information, the application automatically searches for and clearly displays the password of the targeted account.
A simple and effective technique that requires no special technical skills.
Moreover, you can try PASS DECODER risk-free. The trial period lasts 30 days—after which you’ll receive a full refund if you don’t see any results.
In the list of computer programs most used by hackers, we can easily cite this one as one of the most common. The Keylogger, known in French as a keystroke logger, is a spy program designed specifically to steal all of your keystrokes. In other words, when a keylogger is installed on your terminal, it allows its operator to collect everything you are going to type on your device's keyboard. Of course, this includes login credentials. The only concern of this application is that it doesn't require finding a subtle way to install it without the knowledge of the victim on his device. Besides, in a way, this spy program can only be used when the victim is using a physical keyboard. In other words when it is for example a virtual keyboard, it will become useless.
To close this program vulnerability, hackers tend to use what is called screen recorder. Unlike the keylogger which steals your entered data, the latter will simply steal everything that happens on the screen. All of your activity is visually accessible by the hacker who can simply take advantage of it.

Almost everyone uses a WiFi network, however not all WiFi networks are secure and reliable. Indeed, hackers use a technique that consists of deploying a fake WiFi network that monitors the activity of anyone connecting. In this way, hackers can then steal the login credentials of your online accounts. The most impressive thing about this technique is the fact that you don't need a lot of resources to set it up. However, it is still necessary to have a minimum of knowledge to set up everything that depends on the collection of data without the knowledge of the user.

This technique is the most popular that could be used by hackers. The brute force attack is both a simple and a complicated method. Its operation is very simple:
First of all the hacker will develop a script capable of processing in an automated way the production of thousands, even millions of combinations of letters, numbers and symbols of all kinds. The idea is quite simply to randomly produce several types of passwords. Each production will be tried as a login so that your real password can be determined.
This is a technique that works well but it requires a lot of skill in setting up the automated script. If it works correctly, it should be taken into account that the duration of the brute force hack will depend on the complexity of the password you want to hack.
Social engineering or social engineeringis a practice outside of piracy as such. Indeed it is not a technique of computer hacker in its own right. Let's say rather that it is a technique which consists in using a certain rapprochement with its target in order to extract information from it. First of all the hacker will try to establish some relationship between himself and the person who is targeted. In the exchanges, he will ask certain questions likely to allow him to have personal information. This often goes on the basis of games or casual conversations. Once this information has been collected, it will then be studied to deduce data that may be connection identifiers. This is one of the most used methods by hackers nowadays. There is no solution to guard against it because it is easier to use social ties to deceive vigilance. However, this does not in any way guarantee the success of the technique.

The Spidering Attack strongly resembles the previous technique. Indeed, in these two techniques, whether Social Engineering or Spidering, it is first necessary to become familiar with the targeted person. The objective, as mentioned above, is to establish links in order to be able to collect data. What differentiates this particular technique from the first one we described above is the fact that this one is much more thorough. Indeed, it takes much more time and needs to be as precise as possible since it requires more sensitive information. Hackers use the Spidering Attack to typically target businesses.

Ransomware, also known as ransomware or ransomware, is the most worrying threat in the field of computing and telecommunications. These are the threats that over the past 10 years have caused the most damage. For some years, the US government considers users of this kind of virus software as terrorists.. This helps deter hackers by demonstrating the dangers of this program. But contrary to popular belief, it is not only used for the purpose of holding a computer system hostage and demanding payment of a ransom. It has been repeatedly proven that this computer program is also used to collect sensitive data on the terminal on which it was installed. Namely that it can even be used against smartphones.

SIM Swapping is not a hacking technique strictly speaking but more a technique using a security breach. Indeed, the SIM Swap makes it possible to take advantage of the vulnerability of the online services of the mobile telephone companies. It may happen that a customer of a telephone operator needs to make a change of electronic chip and when this happens, the latter now has a new chip which contains his number. This is exactly what benefits the hacker. Indeed, in the SIM Swap technique, we have a person who calls the mobile phone customer service of his target. Subsequently, he pretends to be a user he wants to hack by providing some information of a personal nature. Online identity theft is something pretty simple these days. When the theft is successful, the criminal will ask the telephone operator to transfer the phone number of his target to another SIM card. The new SIM card will then be delivered to an address provided by the hacker. From that moment, the hacker has access to your phone number. As we all know, our social media accounts are often linked directly to our phone number. Whether for our social media accounts are often linked directly to our phone number. Whether for our social media accounts are often linked directly to our phone number. Whether for two-factor authentication or basic password reset. At this point, you can just imagine that your Snapchat account may be hijacked.
There are many techniques for stealing login data such as your Snapchat account password. It is almost impossible to make an exhaustive list of your level of knowledge, your IT resources and your real-time needs. On the other hand, you can very easily find a technique that suits you.
Understanding basic security principles is crucial for protecting your Snapchat account from hackers. Follow these seven essential measures to enhance your Snapchat account security and prevent unauthorized access.
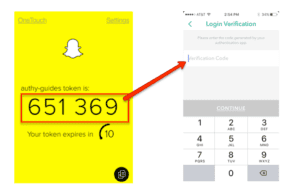
How to Enable 2FA on Snapchat:
Open the Snapchat app on your mobile device.
Tap your profile icon or Bitmoji in the top-left corner.
Select the Settings (⚙️) icon in the top-right corner.
Scroll to and tap "Two-Factor Authentication" or "Two-Step Verification".
Tap "Continue" or "Enable."
Choose your preferred verification method:
SMS Text Message: Receive a code via text (convenient but less secure than an app)
Authentication App: Use Google Authenticator, Authy, or Microsoft Authenticator (more secure, works without cellular service)
Important Reminder: While these seven security measures significantly reduce your risk, no security method is 100% foolproof. If you lose access to your account despite these precautions, password recovery tools like PASS DECODER can help legitimate users regain access to their own Snapchat accounts through secure password recovery methods.
Hacking into someone's Snapchat account without their consent is illegal and punishable by law. Engaging in unauthorized access to someone's account violates privacy laws and can lead to severe consequences.
Yes, there are several measures you can take to enhance the security of your Snapchat account. These include using strong and unique passwords, enabling two-factor authentication, avoiding clicking on suspicious links or attachments, limiting exposure of personal information and staying informed about potential security threats.
No, the hacking techniques discussed in the article are not ethical. It is important to emphasize that hacking into someone's account without their permission is illegal and unethical. The article provides information for educational purposes only and strongly advises against engaging in any illegal activities.
If you suspect that your Snapchat account has been hacked, you should immediately change your password and enable two-factor authentication if not already enabled. Additionally, you should report the incident to Snapchat support for further assistance and take steps to secure your other online accounts.
Despite various techniques and tools available, hacking into someone's account is illegal and unethical. It is essential to respect privacy laws and refrain from attempting to gain unauthorized access to accounts.