3 reliable ways to hack into an Instagram account
1- The Decryptor Pass Method
Pass Decryptor is software that can decode any Instagram code. With this computer program, you can access any Instagram account as many times as you want. you just need to know the username of the person you're targeting, and in just three steps you'll have the right things for you. This program has the merit of being safe, effective and fast. Not only does the person you want to hack it won't even realize that you have access to their password, but, you won't risk leaving a trace of your passage. And to do this, you simply have to follow the three recommended steps:
1 – Install the app on your device.
2 – Follow the set-up instructions
3 – Insert the username of the person you are targeting into the search field and validate the search.
in less than a minute you will automatically have access to the password of the No one. One of the advantages of this tool, which makes it easy to bypass dual-factor authentication. In this way, you don't have to to have physical access to the terminal of the person you want to hack.
You can try this tool for 30 days by clicking on the following link https://www.passwordrevelator.net/en/passdecryptor
Just be aware that the method is guaranteed or refunded.
2- The "forgotten password" method.
There is another fairly simple method that is available to everyone and does not necessarily require technical knowledge of computer science. On the Instagram login space, there's the small section titled "Forgotten Password." All you have to do is enter the login credentials of the person you want to hack. Then you click "forgotten password." Automatically Instagram will offer you a password reset that will be done either by SMS via the phone number associated with the account or by email address. If you're lucky enough to have access to the mobile phone or email address, you can easily reset the password and adapt it as you want. Instagram also offers a reset with a connection through the Facebook account. This means that if you can access his Facebook account, it will be very easy for you to access his Instagram account. However, if you cannot access his mobile phone, email or Facebook, note that this method is lost in advance. Moreover, even if it works, the hacker will quickly realize that his Instagram has been hacked because he will not be able to access it. In addition, you will be located to see identified because your IP address will be affiliated with the entire operation.
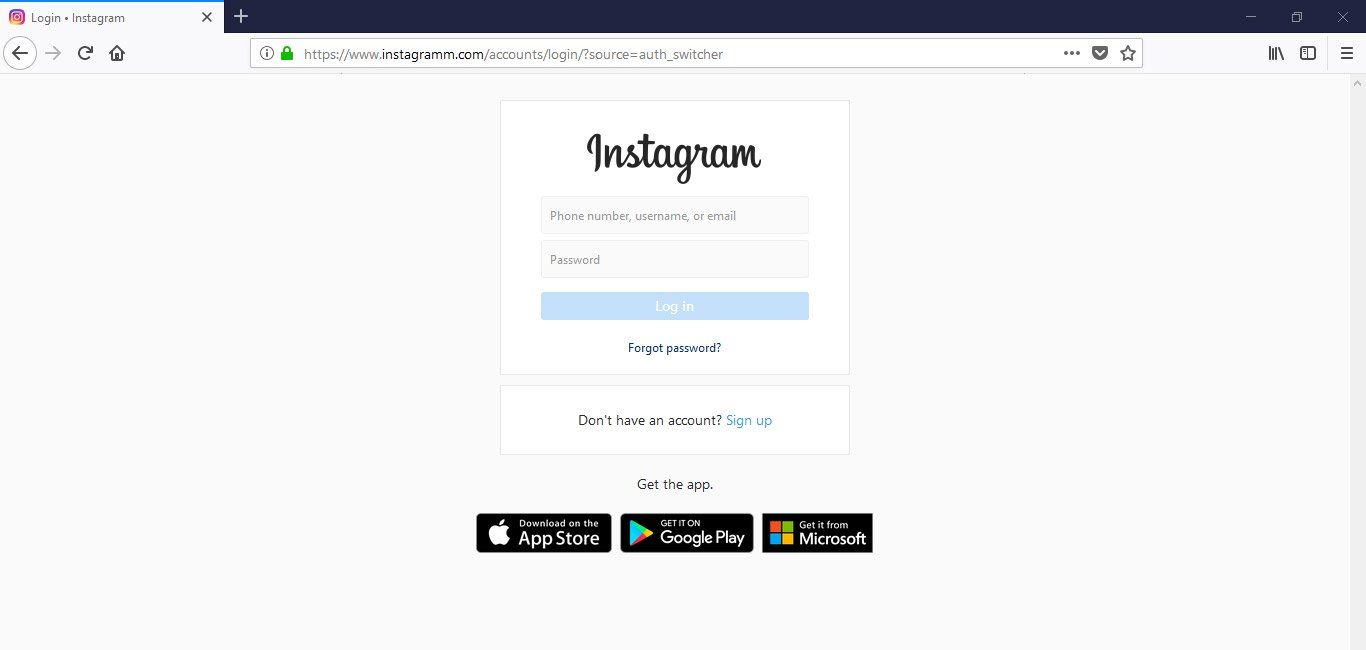
3- the phishing method
Phishing or phishing is one of the most reliable method after Decoder Pass. Indeed, it is clear and leaves no trace without forgetting its effectiveness. However, it requires a good knowledge of the computer tool without forgetting the programming. Indeed we will have to design a fake website, which resembles that of Instagram. Then you will have to attract your target to this site through a link that you may offer by message or email. If he takes the bait and tries to connect, he'll think he's on the Instagram login page. He will then write down his contact details in an attempt to connect to his site. If this happens, you can quietly retrieve his contact information which you can use later without the latter noticing. The problem with this method is that it will require a lot more effort, technical and practical knowledge, not to mention a little financial effort because you will have to, remember, host the active site you want to use.
Now access an unlimited number of passwords!