
3 practices for better safety
1 – Adopt a password management policy
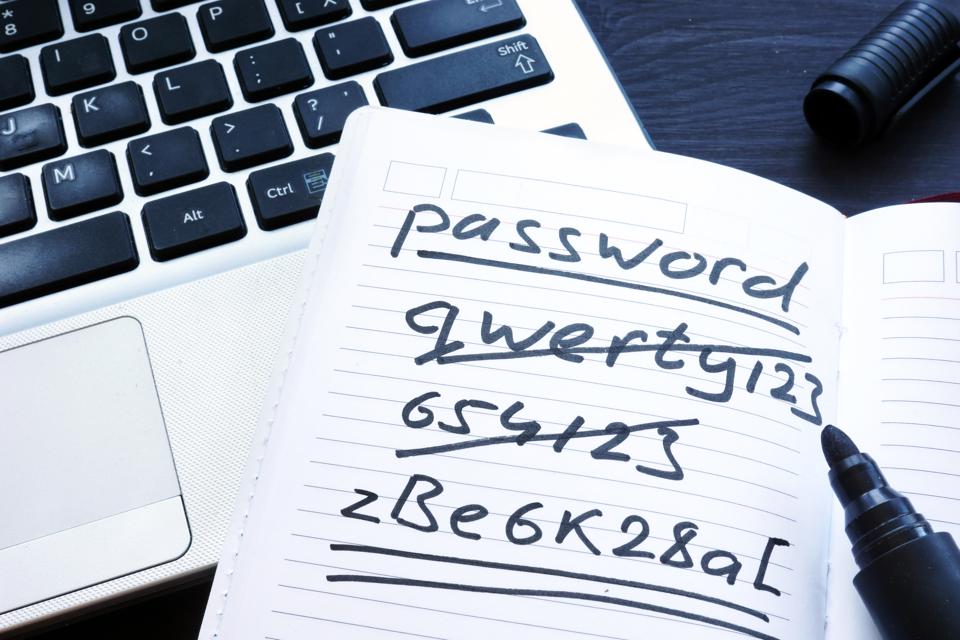
The password is essential for protecting the computer system or terminal. This is the first obstacle that and hacker faces when he attempts an intrusion. However, the mismanagement of passwords today the easy task to cyber criminals. This seems quite understanding when you have to use passwords on multiple accesses or multiple accounts.
The work becomes quite difficult, in fact, average users tend to neglect the diversification of the password depending on the account used or the requested access. Yet it must be a reflex. Because if the same password is used in all accesses, then it would be enough for the hacker to discover it to have access to everything. It is for this reason that tools exist to facilitate the management of different passwords in accordance with the different accesses that are requested. The password manager. They should be used because they are created to make it easier to use multiple passwords for a single person. This reduces the possibility of forgetting, but also allows to be able to consist of solid passwords without having to confuse them or forget them.
The password manager also protects you from certain malware such as keystroke recorders, because with each connection the fields automatically filled.
2- Using the cloud for backups

It is important to be able to safeguard your information. Especially at a time when ransom programs are proliferating more and more.Back-ups on somewhat external physical hardware can be useful in case of computer attacks.However you will not be immune to a potential material crash. While in the cloud, security is improved and you will be able to access your data from any device for a transition if your computer system is available. The advantage of online backups is not only material but also secure.
3- Make updates

Some high-impact computer attacks have been caused by the neglect of updates. The advantage of their deployment is that they reduce IT risk by fixing security vulnerabilities. That is why they are constantly recommended. It's even better to schedule on ending the automatic update."Most computer security experts recommend updating your software or operating systems quickly. But users may be tempted to wait a bit before performing them, to be sure to get feedback from other users, ensuring the reliability and security of this new update.
This is a mistake too often made. It is important to follow the recommendations of software vendors and make updates when required. Why? Simply because installed software can contain security vulnerabilities that hackers can exploit. Software solution developers have a strong interest in fixing these security vulnerabilities when they are detected and launching an update procedure. But sometimes users aren't always aware of requests for software updates. Users often turn off app notifications or don't use certain apps for a long time, so no update alerts are released. described the security company Avira, in a recent blog post.
Now access an unlimited number of passwords!