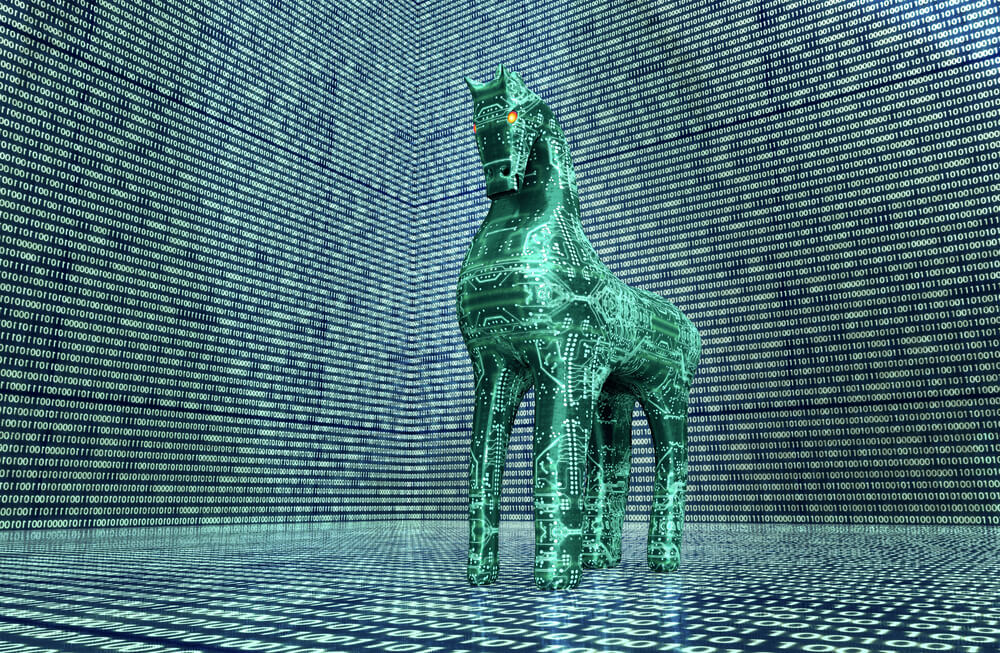
How do I use a Trojan horse?
The Trojan horse, or the Trojan or Trojan in English is a malicious computer program designed for the purpose of espionage and illegal data collection.
In most cases, this program is installed by the victim herself inadvertently or even without his or her knowledge. This software allows its designer to control the terminal in which it is installed.
This article will interest you too: Malware that puts our computer security at risk
To get him into terminal, the hacker sends it to his victim in the form of an e-mail, in the majority of cases. The software is in the attachment and the user will have to open it. The file goes so discreetly that the victim will not go account. Once installed, the spyware will move into the less visible from the operating system.
The installation file will be hidden in a other file that is quite normal such as a game or a player multimedia.
Automatically, the spear software. he can run immediately or later. It all depends on the programming made by the designer. It borrows a generic name to melt into the program mass and don't draw attention to it.
The Trojan horse will send a signal to his designer or its user. In this way, the latter will be able to set up other programs created a data collection machine that will collect to the new program
In accordance with the program, the hacker will be able to:
– explore and monitor the victim's device for information such as login credentials (passwords, usernames) or bank identifiers such as bank codes, etc.) and ship them to any outside terminal;
– damage data to put the data into harm how a PC works or renders it ineffective;
– launch automatic actions of the terminal, for example examples, mass spamming messages;
– create a backdoor for the hacker who can then break into the device to study documents or even take control of the machine.
Note that the original Trojans are quite to bypass anti-virus programs. These are programs that do not replicate unlike worms and will not infect others Programs. Anti-viruses still have a hard time detecting Trojans because their design is quite special.
A famous Trojan horse has been making a name for itself lately. This is the "Pegasus" malware famous for its sophistication. Because once set up in a mobile, be it iOS or Android, this malware is able to copy all the data desired by its user, using different servers.
Apparently he's able to impersonate even the phone and access the hack victim's cloud. The power is at the level where it is even able to bypass the famous dual-factor authentication system. Even if its designers claim to have created it only for governments to fight terrorism, it does not prevent that such software could be used for many other things.
Now access an unlimited number of passwords!