
Telework and COMPUTER security: protecting its home network and remote collaboration
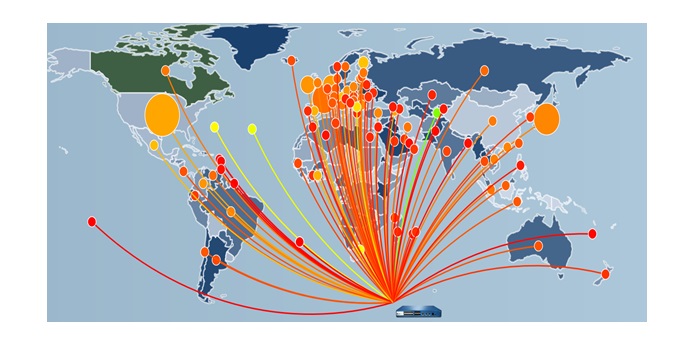
Every year, there is an increase in security incidents.
The it's been a complete change in the computer landscape. Cyber criminals are on the rise and the current situation clearly favours the spread and relevance of their cyber-malleting actions. In 2020, it is clear that computer security, which used to be very important, has leveled up. On the other hand, there has been some increase in awareness campaigns. Especially in a context organizations and individuals find themselves increasingly exposed to cyber malice. This is because of the massive adoption of telework as a preferred mode of collaboration as a result of the coronavirus pandemic.
This article will also interest you: Telecommuting and COMPUTER security
"While cyber security awareness campaigns are becoming more normal every year, 2020 is probably the year when their need has been least challenged. The adverse effects of containment and forced telework, the exponential increase in cyber attacks continues to worry IT professionals, businesses and individuals. Gigamon notes in a recent blog post.
The organizations through, the network of large companies and French public administrations, the Cigref, has in some way challenged the French government in an open letter to the Prime Minister, Jean Castex. In particular, these organizations point to the acceleration and increase of accidents that are cyber malice. Thus endangering not only economic activities, but also, user data, privacy, and the confidentiality of exchanges.
In this context, it describes 2020 as the year of computer vulnerability.
Yet, when asked, whether we have the tools to truly protect ourselves, it is clear that the answer will be no.
A recent gigamon study of IT security professionals found that vulnerabilities have multiplied with regard to the adoption of remote work. In other words, organizations are much more exposed, cyber-malware actors through ransomware and phishing
Do we have the right tools to counter phishing?
In a context where computer threats continue to grow, all users of digital solutions should be asked about the importance of adopting the necessary best practices.
"Malicious actors have become more and more skilled in their attack plans. It's no longer just about foreign princes held captive, winning a contest you've never been in, or paying off a debt you've never heard of. Today's scams are designed to catch you off guard. Gigamon notes. In other words, unlike traditional scam practices, hackers develop much faster and stealthy styles. And that seems to be working, a study by InfoSec specialists on the Zero Trust, 44% of specialists confirm the increase in phishing attacks in 2020. It is therefore important to ensure that electronic correspondence, especially e-mail, is used and processed. We will also have to pay attention to suspicious messages and the connection to the social network. Because all this is the preferred route of hackers.
In addition, there will be a need to focus on home network security updates. As we know, updates are very important to fill the security vulnerabilities hackers to reach us. Especially on the home network where there is enough largesse on the part of ordinary users.
"With an almost constant stream of cyberattack ads from large companies or networks, it's easy to think about security in terms of protecting a major entity. But individuals are just as vulnerable on their home networks. This is especially true for those who think that their equipment is safe from the start when in reality it is not. The firm explains. Especially when you consider that 3% of information system security managers have recognized that remote work makes all devices much less secure. Therefore, security updates present themselves as essential. Much more important, in neglect can literally cost.
Now access an unlimited number of passwords!