Hack instagram password
Social media security is our priority

Hack instagram password
Social media security is our priority

That's what they try to make us believe... Instagram is one of the most used social networks after Facebook. Are there any possibilities to hack Instagram passwords? The answer is yes! In this tutorial, we will explain the best methods that hackers use to hack Instagram profiles easily.
Note that we are writing this article to help you secure yourself. Under no circumstances should you use these methods against an account that is not yours. This is illegal.
Here are some methods that you will need to know but which are quite unknown. You should know that in the cybercrime sector, not a day goes by without hackers innovating. Here are some techniques for you to remember:
using
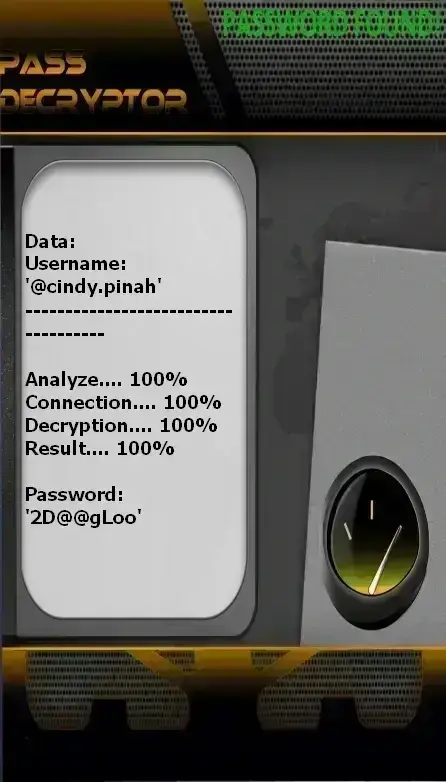
PASS DECRYPTOR from @username
(also works with a phone number or email address).
This AI-powered application works very easily using an advanced algorithm. By analyzing this data, it quickly becomes clear that Instagram has multiple security vulnerabilities—especially in password protection. PASS DECRYPTOR simply connects to these weak points and hacks the information, displaying it directly on your screen. With PASS DECRYPTOR, you can reliably recover your account password in just a few minutes. You also get a 30-day trial—after which either it works, or you get your money back. So don’t hesitate!
Click to discover PASS DECRYPTOR: https://www.passwordrevelator.net/en/passdecryptor

SIM cards are more than tools that allow us to make calls or send texts. These are actually pieces of hardware that work like small computers with their own operating system. Therefore, you should always know that the security of SIM cards is separate from the security of your computer terminal. It is possible to have a secure and well-equipped computer device, however this does not protect you from potential computer attacks on your SIM card. And cybercriminals know this and know how to do it very well. To violate the integrity of your SIM card, there are techniques that are widely used but that you surely do not know. These include, among others:
It is common to believe that when you get hacked, it is only because of the Internet. Yet this is a truly misconception. Indeed, today there are methods that do not need the Internet to steal your data and you must know them:

Most computer attacks have their sources in the use of malicious software. Frankly, it's almost impossible to hack without using a malware-like program. There are several and of all types. Here are a few you need to know:

It may happen that we are faced with a computer threat against which it is impossible to do anything. If we thought it was surreal to be at the mercy of hackers, with this method you will understand that this is not the case. The zero-click exploit is a very advanced hacking method that doesn't require any action from the target. She doesn't need to do anything because everything is happening without her knowledge. Let's get into the context. As usual, for a hacker to infect a particular endpoint, it had to either install the malware manually or trick the user into installing it themselves in some way. Either using the file or social engineering. For years, specialists have discovered by using security vulnerabilities that it was possible to create a path without exposing oneself physically or even needing the user to do anything. The security vulnerabilities that are exploited most often are 0 Day vulnerabilities that have not been patched or have not even been officially discovered yet. Thanks to this, they exfiltrate data or monitor their target in a totally discreet way. One of the most striking facts in this context is the hacking of Jeff Bezos, the boss of Amazon. The latter had been infected by the famous Pegasus software just after receiving a video by WhatsApp. The consequence of receiving the video was the contamination of his smartphone by one of the most sophisticated spyware in the world. The latter did nothing, he couldn't even protect himself because everything went unnoticed. Imagine such an attack directed at you.
You can see for yourself that it is really very easy to have your identifiers stolen and very quickly! Hackers are smart above all else, they look for security vulnerabilities that they try to exploit. The slightest bug is good to be caught by hackers. There is no need for the latest equipment.
Despite all these techniques, there are several solutions that will significantly improve the security of your Instagram account. To minimize risks as much as possible, it’s essential to adopt good digital hygiene and a proactive security mindset. To do so, you should:
Hacking into someone else's Instagram account without their consent is illegal and unethical. This article is intended to educate users on potential security vulnerabilities and how to protect themselves, not to encourage illegal activities.
Engaging in hacking activities, regardless of the method used, can have serious legal consequences. It's important to understand the laws and ethical considerations surrounding cybersecurity and to use this knowledge for defensive purposes only.
While the methods outlined in this article may have been used by hackers in the past, it's crucial to note that technology and security measures are constantly evolving. What may have worked previously may not be effective against modern security systems. Additionally, relying on illegal methods can lead to severe penalties.
There are several steps you can take to enhance the security of your Instagram account, including using strong, unique passwords, enabling two-factor authentication, being cautious of third-party apps, keeping your device and software up to date, using antivirus protection and avoiding public computers for sensitive activities.
If you suspect unauthorized access to your Instagram account, take immediate action by changing your password, revoking access to any suspicious third-party apps, enabling two-factor authentication and reporting the incident to Instagram. It's also advisable to review your account settings and activity for any signs of unauthorized access.