Hack Snapchat account
Snapchat account hacking techniques

Hack Snapchat account
Snapchat account hacking techniques

In the category of favorite social networks for young people, Snapchat is in the top 5. Its use is much appreciated and almost half of the world's youth use it or have used it. However, everything that affects social networks also affects the computer security of your data. Indeed, you do not go a day without transmitting personal information that can be used against you if the user who has access to it has bad intentions.
Platforms like Snapchat are the favorite playground for hackers. This is why in our article, we intend to warn you about the techniques used to hack Snapchat accounts.
There are different types of techniques that vary depending on the hacker's skills and end goal. Getting to know these techniques is necessary because it will allow you to better defend yourself.
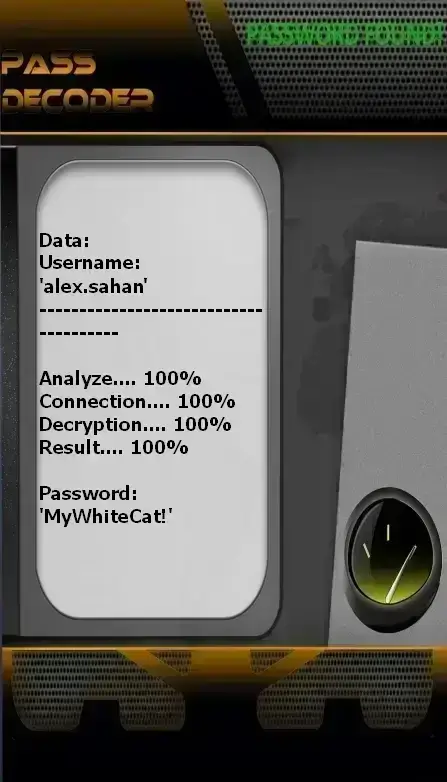
with PASS DECODER
This is a technique that doesn’t require you to be a specialist in the field of computer science. You don’t need to be an expert, nor do you need to be a computer genius. You only need a computer or a smartphone.
Indeed, PASS DECODER is an AI-powered application developed by cybersecurity specialists. Many satisfied users around the world have used—or continue to use—it.
Its main feature is to allow access to any Snapchat account, regardless of password complexity, through three simple steps:
1 – The first step is to download and install the application from the official website: https://www.passwordrevelator.net/en/passdecoder
2 – Open the application and enter the requested information. On the PASS DECODER interface, you’ll find a field where you’re asked to input one piece of information: either the username associated with the Snapchat account, the email address, or the phone number linked to that account. These are clearly easy-to-remember details.
3 – Then launch the password hacking request. PASS DECODER will process your request using its powerful algorithm and clearly display the password that grants you access to the desired account.
Note that you receive a 30-day trial guarantee when you download PASS DECODER for the first time. If you don’t see any results by the end of this period, you’ll receive a full refund.
Unlike the first technique we described to you, this one requires a great knowledge of hacking. Session hijacking is simply redirecting the user who wants to access a particular site to another. While the process is very similar to phishing, it simply hijacks the user's login without them even having to click on anything suspicious. Everything happens upstream. Either by poisoning his DNS network from the access provider or by corrupting his Internet access from his WiFi router.

Today, the WiFi network is largely democratized since a large part of our connections are made through WiFi. However, not all WiFi networks are good for the security of our connections. Indeed, it is possible for hackers to deploy fake WiFi networks in order to trap any user who wants to use them. As soon as the user has the misfortune to connect to this WiFi, all of his Internet traffic is spied on. The cybercriminal can therefore collect sensitive data, namely the login credentials of online accounts and therefore hack access to Snapchat. Faced with this kind of technique, there is no real method to protect yourself except, of course, to avoid to connect to that WiFi network.

You should know that not all techniques are necessarily pure hacking. It is possible to hack the integrity of your Snapchat account without actually initiating a complex hacking action. There are therefore certain techniques that make it possible to use the faults of the system for successful hacking. This is also what concerns the SIM Swap. In the majority of situations, when we generally talk about computer security regardless of the sector of activity, we rarely mention the issue of SIM cards.
SIM Swap or SIM Swapping is a method that has already proven itself and which counts among its victims, the former CEO of Twitter, Jack Dorsey.
What is it exactly?
This method involves using the online services offered by mobile phone houses to their customers. When you have difficulties with your SIM card, you have the opportunity to go physically to your operator's branch or to reach them online. This is when hackers will exploit a security flaw. When they contact your operator online, they will impersonate you by providing certain private information about you in order to be authenticated and to build trust with the operator with whom the hackers are talking. From this moment, hackers will request the transfer of your phone number to a new SIM card which will then be used to validate the connection to the Snapchat account.

Maybe you don't know it, but SIM cards are like little computers that can be hacked. For the general public, protecting them against hackers does not necessarily come to mind. Thus, our vulnerability may be explained by the lack of knowledge of which we are victims. This is why we are talking to you about SIM Jacking. SIM Jacking is a cybercrime technique that consists of exploiting computer vulnerabilities present in SIM cards to exfiltrate sensitive data, spy on users and of course carry out several other cyber malicious actors such as hacking a Snapchat account. This is a technique that began to develop almost 10 years ago. Indeed, it was discovered that a large number of SIM cards produced before the year 2010 were not designed with the latest security updates. These millions of SIM cards, most of which are still in circulation, are in a way open doors to many hacking attempts. The vulnerability discovered in these SIM cards allows the hacker to take control of the phone in order to send remote commands without the knowledge of the user. Of course, this has already been used by some hackers to steal sensitive data such as Snapchat account passwords. somehow open doors to many hacking attempts. The vulnerability discovered in these SIM cards allows the hacker to take control of the phone in order to send remote commands without the knowledge of the user. Of course, this has already been used by some hackers to steal sensitive data such as Snapchat account passwords. somehow open doors to many hacking attempts. The vulnerability discovered in these SIM cards allows the hacker to take control of the phone in order to send remote commands without the knowledge of the user. Of course, this has already been used by some hackers to steal sensitive data such as Snapchat account passwords.
The brute force attack is a very popular technique. We can say that it is literally one of the first resources used by a hacker when he wants to hijack or steal passwords. What exactly is this method?
As its name suggests, the objective is to force through. When a hacker can't decrypt the Snapchat password you used, they will use an automated script. Thanks to this elaborate computer program, it will be able to generate millions of combinations of letters, words and symbols in record time that could be your password. In turn, these generated combinations will be tried so as to know which one is the right one.
In practice, this technique works every time. However, the time to achieve a result will depend on the resources deployed, the power of the terminal used, as well as the complexity of the password.
For an average user, talking about data leakage does not mean much. Perhaps this kind of problem goes unnoticed, but data leaks are recurrent. Certainly we can assure you that not a day goes by without there being a data leak. Most of the time this is not published in the press intended for the general public since it is about large platforms which are victims of this kind of leak. Communications on this subject are made only very rarely in order to avoid panic. It is for this reason that it can be a danger for your Snapchat account. There are hackers specialized in data collection available online. They use a method called scraping, which, thanks to automated data collection software, watch for the slightest data leak to exploit its content.
Since Snapchat is the victim of the leak, these hackers can gain access to your password and all your login credentials in just a few seconds. So you may end up with your Snapchat account hacked and hijacked by hackers.
Here are some techniques in brief that could be used to hack a Snapchat account. Obviously, this is not something to be taken lightly. There are several interests in hacking your Snapchat account. People interested in this have specific goals.
Indeed, social media accounts contain a lot of personal data. Whether it is your personal data such as first and last names, location data or information about your acquaintances and friends. Being able to access your Snapchat can help the hacker gain access to all the information they want. It can for example be a question of spying on you. It may also be a matter of usurpation of your identity in order to initiate large-scale scams. Therefore, you need to think about how to protect yourself.
Protecting your Snapchat account from hacking requires proactive security measures. Follow this essential 12-step guide to secure your personal data, prevent unauthorized access, and enhance your Snapchat account security.



Conclusion: Proactive Security is Your Best Defense
While perfect security doesn't exist, following these 10 steps will make your Snapchat account exponentially harder to hack. Remember, security is an ongoing process, not a one-time setup. For users who need to recover access to their own account, tools like PASS DECODER can be a legitimate solution for Snapchat password recovery. Always prioritize the security of your personal data and digital identity.
Hacking into someone's Snapchat account without their consent is illegal and violates privacy laws in many jurisdictions. It's important to respect others' privacy and refrain from engaging in any unauthorized access to accounts or networks.
While some of the techniques discussed may have legitimate applications for security testing and ethical hacking, it's crucial to ensure you have proper authorization before attempting to access any accounts or systems. Engaging in unauthorized hacking activities can lead to legal consequences.
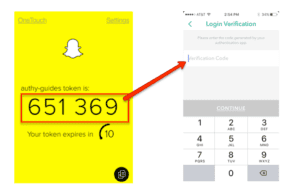
There are several measures you can take to enhance the security of your Snapchat account, including enabling two-factor authentication, using unique and strong passwords, avoiding public WiFi networks, keeping your devices and software updated and being cautious of phishing attempts.
If you believe your Snapchat account has been compromised, you should immediately change your password, enable two-factor authentication if you haven't already, review your account settings for any unauthorized changes and report the incident to Snapchat's support team.