Snapchat password cracker
Methods to crack Snapchat password

Snapchat password cracker
Methods to crack Snapchat password

Most Snapchat users imagine that because the messages are fleeting, the account is secure. However, this is not the case, in fact, messages that people think have been deleted do indeed remain stored on Snapchat servers.
Sad news for those who thought they had total control over their image when sending out daring photos...
Now that everyone knows that Snapchat is not as secure as you think, it also remains very vulnerable to attacks. We can no longer count the number of Snapchat accounts hacked in recent years. It's no wonder when the source code for the application is found on the Internet.
Hacking methods are exploding on the Internet, they are all equally effective. But to successfully crack a Snapchat account for sure, you need to have the right tools... So here are some cybermalware techniques that can be used to control a Snapchat:
passwords using PASS DECODER
PASS DECODER is one of the best AI-powered tools for Snapchat account recovery. It is also the simplest and fastest. Using just a Snapchat @username, it can hack account access and log you in. In fact, this application uses an advanced algorithm—just a quick script execution, and you're in!
You can download PASS DECODER from its official website: https://www.passwordrevelator.net/en/passdecoder

You have to tell yourself the truth, a password usually contains a birthday, the name of your dog, your mom… Hackers use a Learning Solution from social networks. Indeed, they will do research on the Internet using simple means of access such as LinkedIn, Facebook, Twitter... and they will collect as much information as possible about the victim. All you have to do is try different passwords to log into the Snapchat account.

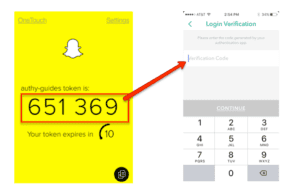
Since Snapchat realized that their social network is not secure at all, they implemented a two-factor authentication protection. This means that when a user wants to connect to his account, he must confirm access via the SMS received on his phone. This protection is not at all developed and confirms once again that this social network is full of flaws and technical defects. The technique of SIM Swappingessentially aims to usurp the identity of the targeted person. One then wonders what could be the point of making this usurpation. It's very simple, the hacker will first gather a lot of personal information about you in order to pretend to be you. This is actually the first step of the method. The second step will consist of calling your telephone operator to ask them to transfer your telephone number to another one that they will have in their possession. He may pretend to have lost his mobile phone or assume a technical failure. Knowing that he has your personal information, he can easily authenticate the identity which is obviously not his own. When your phone number is then transferred to a chip, he can use this number at his convenience. Of course, the majority of our online accounts today are associated with this phone number. The immediate consequences will be that he can easily change the passwords and login credentials of his accounts and use them as he wishes. This is exactly where the danger of SIM swapping lies.

Malware is a computer program that is designed to circumvent the security of computer systems and perform certain tasks to the detriment of the owner of that computer system. In the category of the most popular malware we have the Trojan. It is one of the most widely used hacker apps in the world. This particular one has the possibility of offering several functionalities to its operator. First of all, its particularity lies in the fact that it can camouflage itself in the form of a legitimate application. Hence its name of Trojan horse. Not only can it take on the appearance of a legitimate application buthe can also hide behind a real application and wait patiently to execute and carry out his official actions. Consequently, the user is the very one who, by his lack of suspicion or by his negligence, tends to become infected. When the Trojan horse is installed on a person's computer terminal, several possibilities are available to its operator as we mentioned above. First of all, it has the ability to execute malicious codes on its terminals. Either to create a backdoor or to install a new application. It can also take control of the terminal and perform certain tasks. And the most interesting part, it can of course exfiltrate data and use it for other purposes. The fact that it is a particularly discreet program facilitates its use when you are an expert in the field. The best way to protect yourself against this kind of malware is to have a very good antivirus and not to be in the habit of installing software outside the official application stores.

From now on, the domestic and widespread use of spyware is no longer science fiction or cinema. Indeed, it is not uncommon for spyware to be used to target specific people. Today, there are even slightly lighter alternatives that are commonly nicknamed Stalkerware. To know, we must mention the fact that anyone can be a victim of the use of malicious software. Therefore you are not necessarily safe and this can have an impact on the uses of your online accounts. Indeed, thanks to powerful and even basic malware of the spyware type, it is possible to follow the traffic of an individual anywhere, whether through GSM calls, text messages or even the use social media accounts. Therefore, you must be sure to have an effective antivirus to detect this kind of software. In addition, pay attention to your Internet data consumption. Most often the use of malicious software can lead to high data consumption.

It is a classic in the field of computer hacking. Phishing is most often used to collect data that will later be used to initiate other computer attacks. The technique simply consists of attracting a user via a message that includes a link to a fake website where the latter will be invited to enter their login credentials. When this is done in a general way without a user being targeted in a particular way, we enter the variant of what is called Spearphishing. For this process, the user is targeted in a rather personal way. The message he will receive will be made up in such a way that he is fully confident because he will use codes and information that will allow him to divert his attention. And if the user falls into the trap, he will have his login credentials stolen which will be used against him.

Password cracking will be a rather special technique in the sense that it will be necessary to have the necessary skills and the tools that go with it. Indeed, thanks to a fairly sophisticated computer program, the hacker will try to break your password by trying thousands or even millions of combinations. The duration of this technique may depend on the quality of the password. In other words, the more sophisticated and tough the password, the longer the hacker takes to crack it. Password cracking to a variant known as the dictionary attacker. In this context the cybercriminal will try several combinations. However, the combinations he tries are actually passwords that have been recorded and stored, passwords that he has collected over time.

The DNS attack also known as DNS Spoofing is a technique that consists of violating the integrity of the DNS server in order to hijack the connection of a person or a group of people. The advantage of this computer attack is that it can start from the source of your Internet connection. Indeed, it can happen that cybercriminals manage to infect the caches that allow the web server to operate effectively and efficiently. This poisoning can start from the Internet service provider. This makes it very difficult to protect against it because nothing depends on the user from this moment on. The attack is subtle in the sense that unlike phishing where you have to click on a link for example, here you don't need to click on a link. You just need to connect to the Internet, go to your browser and enter the address that interests you. Since the caches have already been attacked, you will immediately be directed to the bogus website which is under the control of the hackers. And the rest you can easily guess yourself.

You certainly know this expression in the field of computing which says that there is always a fault in the system. This is not a purely ostentatious phrase. In fact, there really is a security flaw in all the systems we use. These security flaws are called 0-day vulnerabilities.
The particularity of these flaws lies essentially in the fact that they are not even discovered by the manufacturers or the users when the computer device concerned is made available. These are security vulnerabilities that can be used without you even realizing it. If today the research methods for these security vulnerabilities have improved significantly, the fact remains that hackers are well ahead of the game in their exploitation. Additionally, there are marketplaces where these vulnerabilities are traded. It is for this reason that it is strongly recommended to always run the security updates that you receive. This may give you the advantage of closing some vulnerabilities.

It is certain that you will wonder how data leaks can endanger your Snapchat account. Let us tell you a fact. Data leaks are situations in which a lot of user information on a platform escapes the controls of the latter. They then become accessible to people who normally would not have access to them. But what information are we talking about? We refer to certain information such as your login credentials. In other words, your passwords and your email address. Which means that if the platform you are using is a victim of data leaks, you can be easily hacked and your login details are at the mercy of criminals. The problem with data leaks, it is the fact that they occur almost at any time. And social networks are usually the first victims of this phenomenon. This is understandable, with the mass of data they must generate and manage, they are unfortunately not immune to some configuration errors. Which means that you are exposed at all times if you are not sufficiently informed about this sort of thing and if you do not have good methods of managing your login credentials.
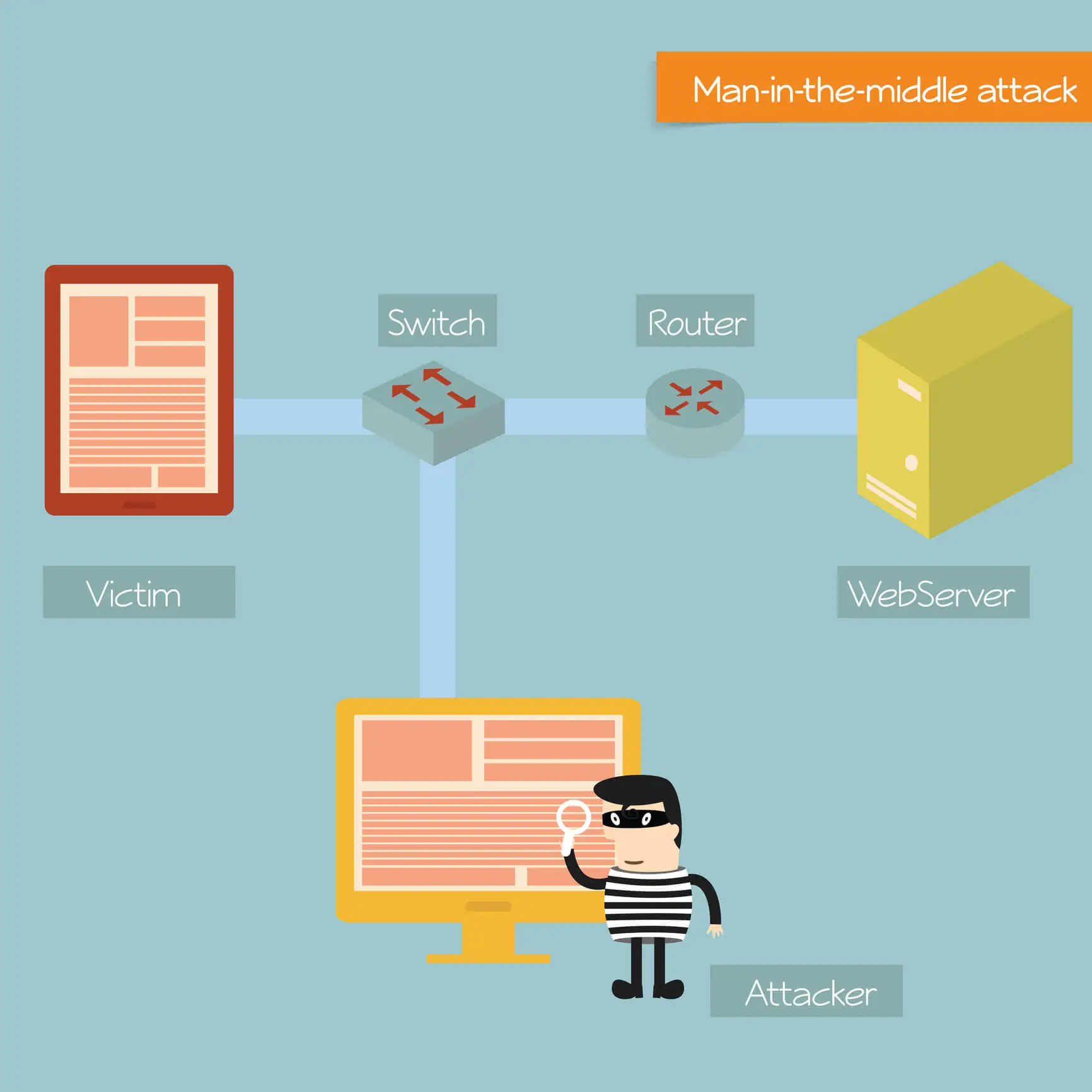
This solution falls into the category of little-known hacking techniques. The man-in-the-middle attack is a concept that is explained by the fact that the cybercriminal will create a bridge between the victim and the server or the terminal with which he wants to order. The purpose of this bridge is to be able to intercept the latter's communications. But how will he do it?
Quite simply by creating a system that allows you to place yourself between your victim and the target server. For this, it is not uncommon for the cybercriminal to use, for example, a fake WiFi network as a point of support. Indeed, it is possible to create a fake WiFi Hotspot. Thanks to this router and some monitoring scripts, you can simply spy on the traffic of all the people who connect to it to have Internet access. In this way, it will be much easier to hijack the login data. However, it must be recognized that it is a technique that requires a good knowledge of computer hacking.
Snapchat is a fantastic communication tool for sending messages and pictures for temporary purposes. Unfortunately, Snapchat is full of major security flaws that can harm their users.
In this second part, we will discuss some computer threats that weigh on your Snapchat account as well as all your online accounts. You should know that cybercrime is on the rise today. Hackers look for any opportunity to break into your computer systems and steal your personal data.
Protecting your Snapchat account from hackers requires proactive security habits and proper device management. Follow these eight essential measures to secure your account and prevent unauthorized access through common cyberattack methods.


Social engineering involves gathering personal information about a target from social networks to guess passwords.
SIM Swapping is a technique where hackers transfer a target's phone number to their own SIM card to bypass two-factor authentication.
A Trojan Horse is malware disguised as a legitimate application, allowing hackers to execute malicious actions on a user's device.
Spyware can be used to monitor and track a user's activities on Snapchat, compromising their privacy and security.
Phishing involves tricking users into revealing their login credentials through fake websites or messages.
Password cracking involves using sophisticated programs to attempt thousands or millions of password combinations to gain access to an account.
A DNS Attack involves hijacking the connection of a user by violating the integrity of the DNS server.
0-day vulnerabilities are security flaws that are exploited by hackers before the manufacturer or users become aware of them.
Data leaks expose user information, including login credentials, making them vulnerable to hacking.
A Man-in-the-middle attack involves intercepting communications between a user and a server to obtain sensitive information.