4 misconceptions about ransomware
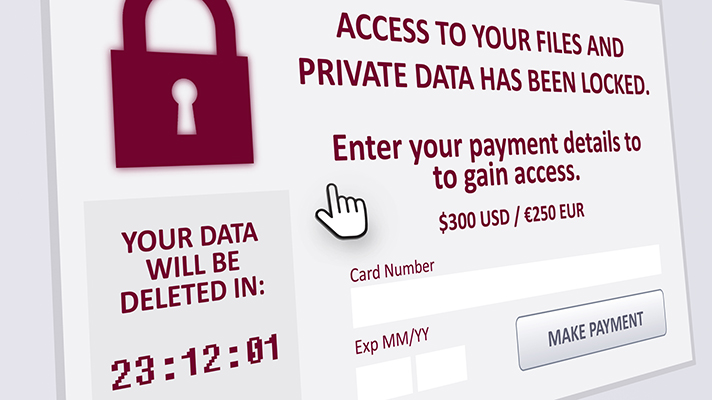
Since 2019, ransomware attacks have become a daily newspaper in the field of computer science.
It is almost impossible to spend a full month without a cyberattack based on this malware being reported somewhere. In other words, ransom software is raging right now and unfortunately everyone is affected.
This article will also interest you: A connected coffee maker can be targeted by a computer attack with ransomware
Whether it is hospitals, industries, small and medium-sized enterprises, large companies, local authorities, all have tasted this bitter fruit. In its recent report (October 2020) Veritas Technologies reported that ransomware-based attacks have increased by 50% compared to last year. This explosion of computer attacks with ransomware has not diminished the conventional wisdom on the issue. Here are 4 that remain the most common
1 – Giving in to cybercriminal blackmail is preferable
With the digital revolution, almost all companies are doing their business on managing several types of computer data. And when this computer data is unavailable for any reason, the company has a hard time functioning properly. In some cases, they can no longer function at all. It is on this fact that pirates merge to initiate their attacks. By preventing companies from accessing giving them away, they are putting pressure on them by demanding a ransom. So far, some people believe it is better to pay the money demanded by cyber criminals. Because basically, the payment of the ransom often presents itself as less expensive than updating the system on its own. Unfortunately, this is a lot of the way the company opts for this alternative. In a study in June 2020, Veritas Technologies reported that 29% of respondents believe that the best alternative is to pay the ransom. Unfortunately, practice has shown that this is not that simple. Indeed, several companies have never been able to recover giving them even after paying the ransom. The computer security company Sophos, one even explained that paying the ransom and you are likely to increase the costs of restoring the attacked system by multiplying them in half. In addition, paying the ransom encourages cyber criminals to continue their activities. This exposes the same company again.
2 – Only people with access to sensitive data are targeted by hackers
Hackers target everyone. Especially the simple employee. All information, as insignificant as you might think, is important to the cybercriminal. An email address, password, bank account numbers, etc. In other words, regardless of the status of the individual. It doesn't matter what business you're in. Also, to think that only the high people placed are the most targeted is a misconception. It is as false as the idea that large companies are generally targeted by ransomware.
3 – Employees can't help fight ransomware
If security experts are unanimous on one fact, it is that the weak link in cybersecurity is the human being. Despite all the tools that hacker has today, it will always prioritize targeting a particular user. "Whether it's viruses, spam or ransomware, users remain the preferred targets of hackers. However, management and employees (untrained and equipped with the right tools) are better able to detect threats and bring up information. Where some security systems will detect threats that once in the company environment, employees will be able to prevent as soon as a threat is identified and participate in strengthening existing protections. Veritas Technologies report
4 – A basic backup is enough to counter the ransomwares
Jean Pierre Boushira, VP Of Southern Europe at Veritas Technologies, replies: "It's a fact, ransomware is a very serious threat and hackers are blithely taking advantage of the climate of insecurity to get their act together. It is therefore essential that each of us know how they work and how to protect ourselves from them at both an individual and a corporate level. Beyond establishing appropriate protection systems, companies need to keep in mind that an effective backup strategy remains their only lifeline once the ransomware has been able to infiltrate the system. Many players associate this principle with simply having a backup stored at a different point from the infrastructure, but to be truly relevant, the backup system must be able to generate an "off-site" copy of the files to prevent malicious encryption attempts. ».
Now access an unlimited number of passwords!
