
How do I hack into a Twitter account?
Twitter is one of the world's most used social networks.
Its popularity makes it famous and attracts lusts. It may have occurred to you to hack into a Twitter account. Your girlfriend's, your child's, an ex or any other person.
You may also be interested in this article: How do I get my Twitter password back?
You want to try, so it's very simple. But what we will expect here is just in the interest of your learning. What you will do with it is up to you. First, note that it is illegal to access a person's Twitter account by hacking it. Put this does not stop you, Twitter can be hacked either by an app or by the technique of phishing.
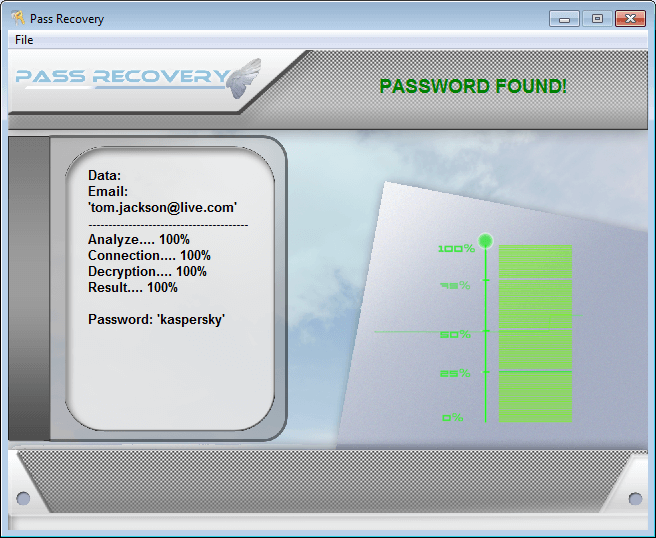
You are able to hack Twitter through an app. For this, we recommend PASS RECOVERY. It is a reliable application that is acquired by thousands of individuals a day.
Download it through this link https://www.passwordrevelator.net/en/passrecovery.php
Install it in three (3) steps:
1) Install the program to be able to access Twitter
2) Open the program and run it on the system.
3) Follow the instructions.
This once operational software will provide you with all the login information you need. Passwords mostly. To can hack multiple times the same account and repeatedly if need be.
Second tip, to hack a Twitter account, you can go through a group of private hackers who sell their services online. They have different 'sites' that you can access through Google. Personal, we cannot judge the effectiveness of this initiative or the legality, but it exists beautiful and well. For a fee, they can or offer to give you access to any account. The risk here, because there is a huge risk, is that these hackers can overtake you and use the access they have provided for their own benefit.
Hack a TWITTER account by the phishing technique directly.
By the software-free method, we'll tell you about phishing.
In a previous article, we talked about this technique. The principle is the same.
It is a popular method for hackers because it allows you to hack into just your loved ones, but also people we don't know. Here you don't need the ID or phone number.
To work on phishing or fishing, it will simply be to create a dummy login page for the Twitter site. In it is necessary to wait for users not too vigilant who will enter their login data to have access to their account online. As a result, the dummy page records useful information and sends it to its creator in a "text file" format to make it easier to use. Having all the login information, the hacker will have access to the account chosen for his operations as he pleases.
In addition, it should be noted that phishing is done with specialized apps. Also it requires a very good mastery of programming, and therefore computer language. This is one of the disadvantages of phishing. May useful for the layman of computer science. Plus it's less accurate. Indeed, this method does not allow to target people in particular effectively.
Now access an unlimited number of passwords!