A cybercriminal alone has attacked nearly 130 organizations around the world
The message fell during the day of June 29.
Kazakh-born cybercriminal allegedly managed to compromise the loan computer systems of 135 organizations around the world.
Following an investigation conducted by the company Group-IB, the identity of the individual behind the pseudonym Fxmsp, the profile of a cyber criminal known for selling computer network access already compromised on several forums. According to reports, these compromised access sales would have allowed him to be a millionaire between 2017 and 2019. These activities have been traced by the Russian security solutions publisher. This allowed them to discover its true identity. Among the victims of this cybercriminal were banks, hotel groups, schools, and even military enterprises in some 40 countries around the world.
This article will also interest you: Hackers looking for security vulnerabilities to exploit
According to the Russian cybersecurity firm, the profile corresponds to the identity of a Kazakh national. It estimates the wealth accumulated by the cybercriminal and his accomplice at a loan of 1.33 million euros, 1,500,000 dollars. Such profitability can be explained by fairly simple methods used by the cyber-friendly to commercialize his criminal skills. To do this he set up an almost industrial system to operate as a business. And even though since last year, the profiles used by these cyber-prisoners have remained inactive, there is a good chance that the latter has redesigned its identities in order to continue to practice in Asia-Pacific. "The first known traces of Fxmsp date back to 2016. At that time, the cybercriminal published a series of messages on Russian-language cybercriminal platforms in the hope of improving its encryption tools, a technique of infecting an entity to divert the inactive processing power of its information systems. It is then used without the consent of its owner to enrich itself by "mining" the cryptocurrency, usually Monero and Ethereum, which operate widely used processors and offer a high level of anonymity. group-IB report.
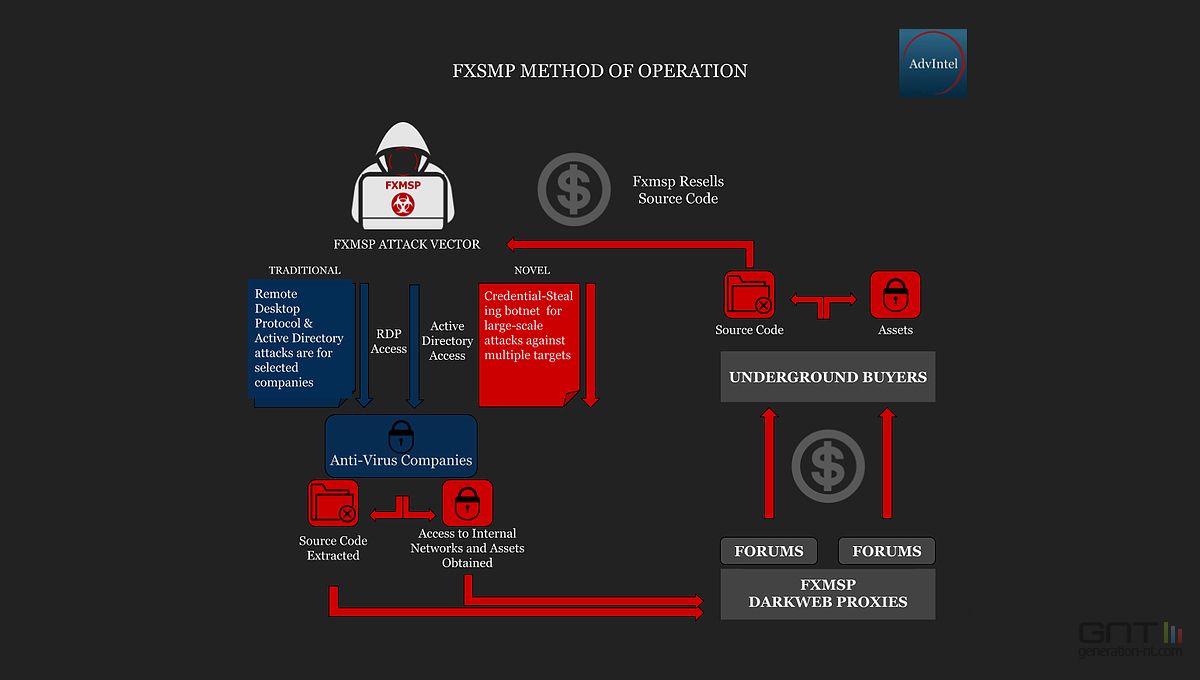
Starting in 2017, cybercriminals are starting to get richer, by marketing access to hacked computer networks. And this is through the initial compromises, going through several phases.First, he is responsible for conducting the reconnaissance and intrusion phases. Then it will ensure the persistence of network and end with the acquisition of administrator privileges thus allowing any intruder to navigate the network freely. Access that will later be sold can be used in ransomware or cryptojacking campaigns. On the other hand, access sales are commonplace in the area of cybercrime. It has become a very profitable and practical business.
The IB Group describes the modus operandi of the cybercriminal in its report: "The technique used by Fxmsp to obtain these accesses is relatively simple. Instead of phishing its victims by pushing them to open an attachment or website containing malicious code, the most common technique, the cybercriminal uses different tools to scan series of IP addresses and identify machines whose port 3389, usually used for remote access to Windows servers and workstations via the REMOTE Desktop Protocol (RDP) , is "open." This gateway allows you to obtain the identifiers of members of the network, whose passwords Fxmsp retrieves using so-called brute force techniques. ».They will then allow him to make automatic attempts to log in, using passwords of people to build up in a weak password collection, a collection that calls itself "dictionary". At the time the hacker is able to identify himself, this allows him to take control of the targeted computer network and disable computer programs without providing security as well as other firewalls. Under these conditions it is able to compromise even the backups made by companies to be sure to have a backdoor on hand in case it gets spotted. As soon as the compromise is completed, the cybercriminal can simply divide the computer network into different areas as he wishes and sell them to the interested parties.
According to the Group-IB study, between 2017 and September 2019, Fxmsp managed to compromise the lending computer networks and systems of 135 organizations in 44 countries. This is possible in almost every industry on five continents, from the smallest to the most powerful.
However, what has propelled the fame of this hacker, is in fact quite symbolic but quite exceptional. The cybercriminal has sold compromised access from three large companies specializing in providing security solutions, in this case Symantec, McAfee is Trend micro. The various actions marketed by the cybercriminal included the source codes of antivirus made available to their customers by these security companies, a sesame for cyber criminals allowing them to discover new ways to circumvent its solutions and this at 300,000 dollars, or 267,000 euros.
Now access an unlimited number of passwords!