Facebook: some hacking methods you need to know
In our article we intend to give you some elements that will allow you to be able to master Facebook account hacking.
We just want to remind you that this information is sent to you in an educational way. Therefore it is excluded that you use them in an illegal context.
Tip 1: use PASS FINDER
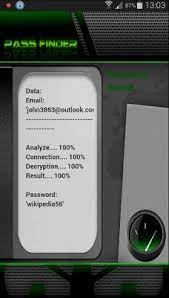
PASS FINDER is a computer program designed to help people who do not have a great knowledge of hacking to practice in the middle. It mainly allows to discover the password of a Facebook account. Why the password? Simply because, when you initiate an account attack, it can be for a Facebook, Snapchat or other account, you have to keep in mind that the objective of this kind of hacking is to discover the login credentials that are:
– email-address ;
– telephone number ;
– and the password.
As for the email address and the telephone number, we have had the opportunity to verify it several times, users tend not to really conceal them. Which makes it pretty easy to get them. However, the password is the login data that is most often difficult to find. Especially if the intended user is in a strong and hard-to-break password composition dynamic. This is where PASS FINDER comes in.
HOW TO USE PASS FINDER?
As we mentioned above, you don’t need to be a hacking specialist to use it. You just need to install it on your terminal. Indeed you do not need to install it on the device of the person you are targeting. You deploy it on your own computer device, then you define the password search mode. It should be noted PASS FINDER offers two search possibilities:
– either by using the email address associated with the Facebook account you are targeting
– either by using the associated telephone number
Once you have chosen the identification data to use, you enter it in the dedicated search bar that the application interface will present to you. Then you start the search. Meaning that the result is guaranteed after a few seconds
WHAT KIND OF DEVICE CAN PASS FINDER BE USED ON?
The application is compatible with several supports. Therefore, you can use it either on:
– a digital tablet;
– a computer ;
– and a smartphone.
In addition, PASS FINDER is compatible with the various most widely used operating systems in the world, namely IOS Android and Windows.
Finally, you must indicate that you have a 30-day trial. At the end of these 30 days, you are either satisfied or refunded.
Download PASS FINDER now from its official website: https://www.passwordrevelator.net/en/passfinder
Advice
We want to tell you an important fact:
As mentioned above, it is against the law to hack the Facebook account of someone other than yourself or someone for whom you have legal responsibility. In other words, you can use the method that we have just described to you. Provided that you remain within the framework defined and limited by law. For example, you can use PASS FINDER to monitor your minor child regarding their activities on the Facebook social network. Because as we know, these platforms do not always offer something holy for our miners. Furthermore, by mastering this hacking process, it will be much easier for you to know, for example, how to better protect yourself and those around you. In particular, you can practice on yourself in order to master the systems. Who knows ? it may be useful to you tomorrow
Method 2 – hacking by traffic interception

Traffic interception will consist in spying on everything that the individual can do when he connects to the Internet. For this there are several means. However, these are techniques that are generally intended for people with good hacking skills.
The most common methods of intercepting traffic are:
– Session hijacking : it consists of pushing the targeted user to connect to a platform other than the one desired by the latter. In this way, the hacker will create a dummy platform that takes on the appearance of the legitimate platform that the target wanted to use. Once successful, he invites the latter to enter his login credentials. Identification data that he can simply recover to carry out his attack;
– The fake WiFi hotspot : an innocuous but very effective technique at an early stage for individuals who are used to connecting to an unsecured public WiFi network. In this process, the hacker will create a WiFi network. Of course the network is not protected by any password. The goal is to trick the user into logging in through fake hotspot . Once this is done, the one heart can quietly spy on its victim’s traffic.
Now access an unlimited number of passwords!