The history of the password is intimately linked to the development of the Internet because the craze of individuals for this new type of technology has awakened hackers who saw it as an opportunity to recover a large number of data and take advantage of it to make purchases for their own interest or steal money from bank accounts. The hacking of email accounts has also been gradual.
The personal password period
For a long time, individuals were able to be satisfied with the first name of one of their children, the name of a particular city or the name of their favorite singer because the threat was not strong. With real pleasure, everyone opened an Internet account with passwords that related to their personal lives.
In 1995, the password had a different place than today with simply a role of personalization of each use by another individual.
With the arrival of the year 2000, the first cases of hacking are reported and even if they remain rare, they arouse the distrust of individuals who no longer know if they really remain safe on the web. While some keep their password as it is, believing that the situation is too infrequent to touch them, others prefer to opt for an alphanumeric password that presents an additional difficulty and then seems to be a sufficient bulwark against hacking attempts. Bank detail thefts are also emerging with the revelation of a lack of security in banking transactions.

Active fight against lack of security
As piracy intensifies, Internet players are beginning to ask much deeper questions about how to limit this phenomenon. The space of the secure space to make its payments online arrives to guarantee internet users that their bank details can no longer be recovered during their online purchases.
At the messaging level, the arrival of messaging issues seems to be sufficient protection. Better information on the risks of Internet use urges each user not to share their credentials and passwords with third parties in order to limit the risk of recovery by hackers.
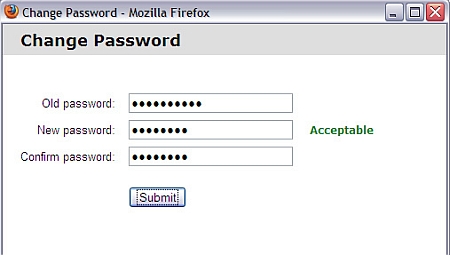
In 2015, the password is questioned because even with a large length, a combination of numbers, letters and special characters, it would only take a few minutes for a hacker to crack it. Alternatives are therefore sought to achieve a much higher level of security.
It seems that a transition to identification by the body is emerging because voice recognition appears to be a good alternative. Even more sophisticated means are also being considered to completely stop the hemorrhage caused by hacking. However, it will be necessary to verify the effectiveness of these measures because the fingerprint quickly showed its limits for security.
You'll also like: Does the password become vocal?
Illustration source: Flickr.
