Crack a GMail password
Get access to GMail mailbox

Crack a GMail password
Get access to GMail mailbox

It is very dangerous to communicate your private information to third parties. Fortunately, you will never do it, on the other hand, you may do it without knowing it...
The lucky beneficiaries of a GMail account know that the Internet is dangerous and full of invisible traps. Hacking a GMail account is not a science reserved for professional experts in the field. Anyone can hack a GMail password in a few simple steps.
GMail is the most widely used email service on Earth, it is also the most fashionable way to exchange secret messages between people. Typically, these are couples who want to gain information by hacking into their spouse's devices in order to test their fidelity. For this they have what is called hacking software.
GMail is very popular as one of the most widely used email clients in the world. The communication tool produced by Google is constantly the target of hackers. The latter constantly use genius and strategies. Here are some techniques that can be used against your device:

account using PASS BREAKER.
This compact program is the easiest way to decode a GMail account. Once installed on your computer or smartphone, it enables the user to access the GMail account. No special technical knowledge is required to use this application—it was specifically designed for quick installation and intuitive use. Any user with basic computer skills can start using PASS BREAKER to hack a GMail address.
After installation, PASS BREAKER will prompt you for the email address of the account you want to recover. A useful feature of the software is its ability to save the decrypted password to a .txt file so you don’t lose it.
You can download PASS BREAKER from its official website: https://www.passwordrevelator.net/en/passbreaker
As you probably know, RFID for Radio Frequency Identification, is a wireless technology. However, hackers have found a way to intercept traffic between the tag and a reader. In this way, they are able to collect information. This is an attack that is possible even if the communication between the RFID chip and the reader is encrypted. For this, it is necessary to use a special tool which works thanks to an induction field which will be adapted to the interception of the signal. However, it must be mentioned, the interception of the message is not absolute. Indeed, if they can extract information, they cannot fully reconstruct the encrypted content of the chip.

In French, it could be translated as port scanning attack. Basically, port scanning is not really something dangerous, quite the contrary. This method is used by information system security managers to analyze the network or computer system in depth. The objective is obviously to determine the presence of security breach that can be exploited by cybercriminals. By observing this, cybercriminals can use it to determine the level of security of a computer terminal or even computer systems. Thanks to this, they know exactly how to proceed. They know what security measures can stand in their way. The rest, you certainly know it. Hackers take advantage of the vulnerability to either install malware or extract sensitive data.

The masked attack is a method of determining which password could unlock an online account based on analyzes of combinations of words and phrases, in some measure of different symbols and characters. While it strongly resembles the dictionary attack, the masked attack does not use a database containing real passwords. Hackers will try to construct passwords from their personal knowledge and understanding of the psychology of the average user.
Take for example a password that starts with a number. At this level, the hacker will try a set of passwords that start the same. This is a technique that requires a lot of concentration and patience. You have to fully understand the target and their way of thinking. The masked attack is much more psychological than technical. Unlike the majority of techniques that seek to crack the password, the hacker here does not use any particular malware.

It is a technique used by hackers to target passwords that are usually stored in a computer system.
It is known, for example, that when a password is recorded in a computer system, it is most often encrypted using a hashing system. We can simply allude to cryptographic protection. It is a means that prevents the determination of the password by any server or other computer system without the decryption key that corresponds to the hash. Hackers know the system and know exactly how to bypass it. They will proceed by registering and compiling several directories which are supposed to store passwords as well as the encryption methods which correspond to the different hashes. Of course, they draw their source of information from databases from previous leaks or hacks. Subsequently, so that the technique can be complex and effectively dangerous, they accumulate their information as well as the decryption keys with the method of brute force attacks.
In practice, this method of hacking isn't just going to steal passwords. It will also store all identifying information that can be harvested. And if it works for one of your accounts, it will try again to hack other accounts belonging to you in the hope that you have made the famous error that the majority of Internet users commit: using the same password on several online accounts. Since all the work is done upstream, the computer attack itself does not take enough time to usurp an account or take control of it. The only downside to this technique is the huge amount of data that cybercriminals have to deal with. But with the evolution of Big Data and all of the related analytics technologies, it's something they can handle with ease.

Called sniffing, it is a technique that consists of analyzing a computer network and all the traffic that takes place there. The sniffing is done with a computer program known as a " sniffer".
To use sniffing maliciously (because it's not really a hacking technique but a network monitoring technique used by network administrators or company managers), the hacker must have physical access to the network to use his sniffer. Otherwise, it can exploit security vulnerabilities that are present in the computer system it targets. Insofar as the first two possibilities are not possible, he will be forced to proceed by using malicious software such as a Trojan horse. There is also the possibility for the hacker to hijack the sniffer used by a company in order to monitor and control its system. It can simply be done.

Computer attacks seek new vectors in order to succeed in data theft or intrusion. One of the most overlooked vectors by average users when using the Internet or computing devices are security vulnerabilities. Typically, security vulnerabilities are found in:
There are several types of security breaches which are classified according to their severity. The most dangerous vulnerabilities are those that are categorized as Zero Days.
These are design flaws, present in IT tools (hardware, software, etc.) and which constitute significant weaknesses in terms of their security. Most often, these are vulnerabilities that have escaped the vigilance of the publisher or the manufacturer of the computer tool. And these flaws exist in almost everything that is computer. They are called Zero Day vulnerabilities to highlight the time imposed for their correction. Which means that as soon as they are discovered, every second is a potential risk because at any moment the victim can be attacked.
The problem with Zero Day security vulnerabilities is that the vast majority of them are not made public. Which means that as users, we are constantly exposed to the possibility of hackers using these security holes to hack us. It may even be that if hackers effectively exploit these vulnerabilities, we can experience computer attacks every day, without us even realizing it. And this until they achieve their goals.

We are in the category of the most regular computer threats. Password cracking is a technique that consists of using several possible combinations in order to find the right password that will allow access to a computer system without the knowledge of its owner. Of course, the formulation of these combinations, which may vary according to the nature of the characters used, whether letters, symbols or even numbers, is carried out by specialized software. For this, almost all professional hackers in this industry have used or are constantly using the password cracking method. It is particularly useful and effective against users who do not have this way of pay particular attention to the wording of their login credentials. The password cracking technique uses algorithms that are developed by hackers using the connection habits of Internet users. This means that, if you are used to creating your passwords using, for example, your date of birth, the algorithm which was developed taking this aspect into account will use information that revolves around you and your date of birth. And that fits chronologically and circumstantially. And that doesn't matter who the user is. The password cracking technique can be time consuming or instant depending on the length and complexity of the password to be cracked. You still have to point out that it
The password cracking technique is clearly different from the dictionary attack. Indeed, the dictionary attack also uses an automated process that allows it to compare a set of passwords compiled in a catalog called a dictionary, to the computer system, in order to determine which of these passwords is the correct one. Their common point is the fact of using software or automated test scripts. However, the difference lies in the information. Where in the password cracking and the combinations which make it possible to create potential passwords are automatically generated by the computer program, compared to a previously determined algorithm, the dictionary attack is content to use a base of already predefined data of passwords formed by unknown persons. In particular a database which may come from a hack or a massive data leak. In the context of GMail for example, Data Leaks are not uncommon.
When using a browser, in particular to access an online account, there is a feature offered to the Internet user which is to save his login credentials. Obviously the majority of us tend to save them because it saves us enough time when we want to connect again. However, it has become so much of a reflex that we forget that these saved passwords are often stored somewhere. Which means that anyone, if they have the necessary skills, can pick them up very easily. Browsers even sometimes offer to discover identifiers in plain text. So if someone wants to access your computer, they can easily steal your credentials and then use them against you.


To crack a GMail password, various techniques can be employed such as password cracking, sniffing, or exploiting security vulnerabilities. However, it's important to note that attempting to crack passwords without authorization is illegal and unethical.
Accessing someone's GMail mailbox without their permission is a violation of privacy and against the law. It's important to respect the privacy of others and refrain from attempting to gain unauthorized access to their accounts.
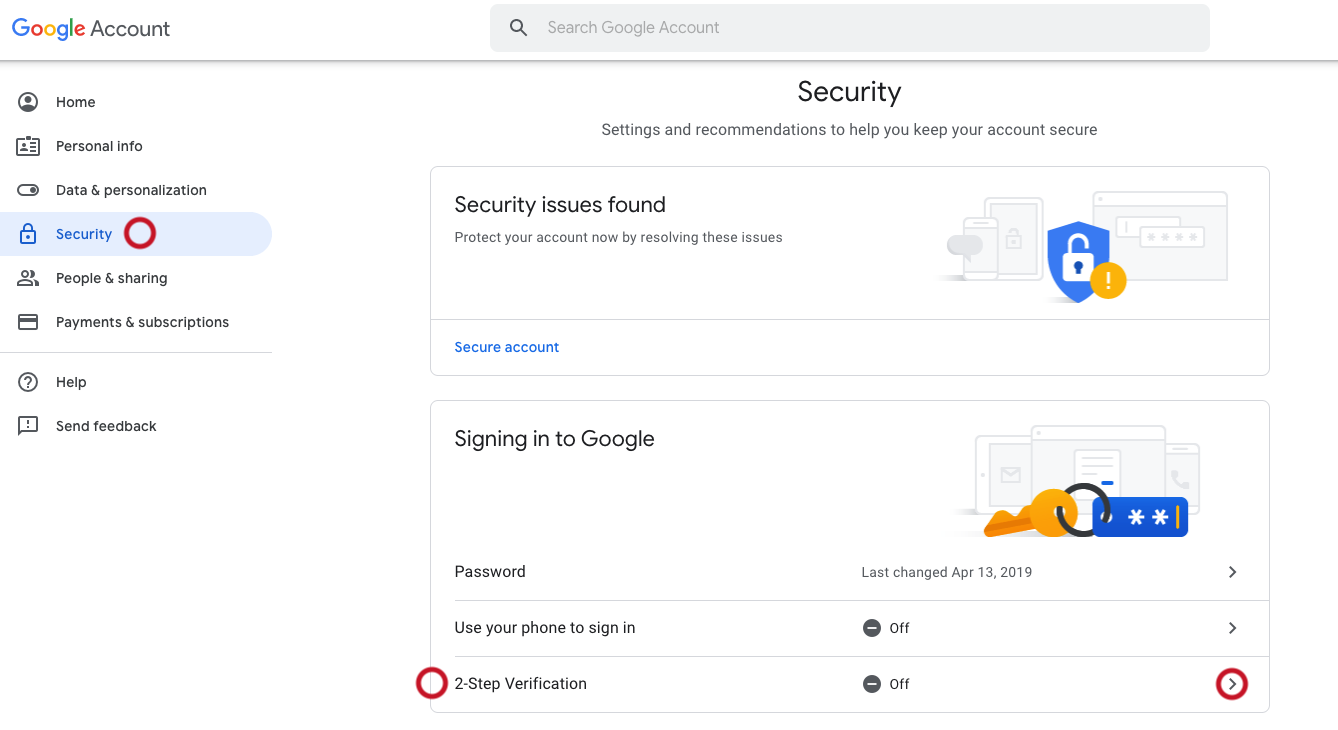
To protect your GMail account, you can take several measures including:
Sharing GMail credentials with third parties can lead to unauthorized access to your account, compromising your privacy and security. It's important to never share your login credentials with anyone.