Hack GMail password
What to do when you are hacked?

Hack GMail password
What to do when you are hacked?

Google can't do anything against password cracking techniques, their role is to provide an email service to its users and do their best to protect them. Computer hacking has undergone a rather dazzling evolution in recent years. If we already know basic techniques used by cybercriminals, there are several that are still unknown and that do much more damage. Here are some of the techniques you need to know and be wary of when adopting good digital hygiene habits.
The advice we can give you is to lie to the secret question answer.

account using PASS BREAKER.
The simplest and fastest solution is PASS BREAKER. This compact application is designed for the general public—no technical expertise required. All you need is the GMail address of the account you want to access, and PASS BREAKER handles the rest. It uses an advanced algorithm to instantly display the decrypted password on your screen.
Developed by cybersecurity specialists, PASS BREAKER is already used by thousands of people worldwide. With this tool, you can hack the password for any GMail account in just a few minutes. PASS BREAKER is suitable for all users—whether you're a tech expert or a complete beginner, you’ll find it easy to use. Don’t wait—try it now! You get a 30-day trial from the moment you install it. At the end of this trial period, you’re either got the access or completely refunded.
Just follow these three simple steps:

The second is phishing, the victim receives in his emails a strange mail which seems official but which asks him to open a Word or Excel document. In this document is a hidden link which, like the small script, will open access to the unprotected device.
It is necessary to have a good level in programming to use this second technique.
As you know, cookies are small computer programs specially designed to facilitate connections between different platforms by reducing loading times as much as possible. We can say that cookies are like beacons that allow a web user to be able to access a website without logging the time he observed during his first connection.
In practical terms, it's a very interesting and useful tool, however cybercriminals have found a way to use it against you. Knowing that cookies serve as a beacon, they found a way to modify the path that these beacons are supposed to indicate. In this way, it is possible for them to divert the Internet user from his real purpose of accessing a particular platform. For example, when you enter gmail.com in your browser, it will be possible to direct you to another website which seems perfectly to GMail when it is nothing more than a fake site.
Thanks to this session hijacking, he then has the possibility of being able to collect your personal data while making you believe that you are logging into your account. Of course you can imagine the consequences...

When we buy a computer device or when we use software, it is rare as a user that we ask ourselves the question of what could be the security vulnerabilities that can be used against ourselves. There are and always will be security vulnerabilities. However, the most dangerous are those that we do not know and that we cannot even anticipate. We are talking in particular about security flaws called Zero Day. Zero Day are security vulnerabilities that are unknown even by the manufacturer of the computer device you are using or software publishers. Today there is a real race to find and work Zero Days.
In this context parallel markets exist either officially or even in the Dark Web. The goal is to be the first to discover these vulnerabilities. Thanks to them, it is possible to initiate almost any type of computer attack. And this is exactly where the danger lies since the user will have almost no means of defending himself against it.
What makes the issue of security vulnerabilities much more complex are so-called 0-click exploits. We are talking about much more dangerous security flaws, whether they have already been discovered or are still unknown. Zero-click exploits give hackers the ability to take action against their targets without them having to do anything. In other words, zero clicks simply open the door and allow hackers to spy on data that can be used against the individual who is being targeted.

Usually, when we decide to talk about hacking, it is clear that we are most often referring to the Internet or the Web. However, the possibility of initiating certain computer attacks without even having to connect to a network is completely neglected.
Today thanks to several discoveries, it is possible to hack into sensitive data using only light. Thanks to an LED light capture device and a computer in particular, a hacker has the possibility of being able to convert these light beams into information. And it actually works when the latter has the right tools.
Using a virus placed in the computer before, the LED used to indicate whether the hard disk is working or not will be used to communicate and transmit binary data. The webcam placed on the computer of the cybercriminal will be able to read these flashes and convert this into digital data.
As we certainly know, cybercriminals do not shy away from anything when there is the possibility of being able to harvest information.

If you are used to using USB keys without really asking where they come from, it is important that from now on you change this habit.
Indeed, USB drives are the most vulnerable and easily usable devices against you. One of the known hacking techniques that uses USB keys is for hackers to infect a USB key and then make it available to unsuspecting users. They may just pretend to have lost them in a public place hoping someone will pick them up. They can also put it in a lot of USB keys for sale. In its USB drives is malware that can be used to log your traffic and hijack your data.

One of the most popular tips when connecting to the Internet is to always make sure that our connection is indeed protected by the HTTPS protocol which is supposed to provide us with the most secure possible data encryption between browsers and web servers. This is important for various tasks such as checking emails, using social networks or just visiting a classic website. This too has the merit of protecting us when we connect to WiFi hotspots. Why is this so important? Quite simply because without this data encryption, we expose ourselves to several threats including a computer attack known as "Sidejacking". The main reason for this threat lies in the fact that it can allow a cyber attacker to very easily access the content of a session after the user exits. It must be said that Sidejacking is a very popular technique in the field of cybercrime.
In a simple way when a connection is not secure, it will consist for the hacker to recover part of the session cookies and to use them within the framework of the usurpation of the identity of the IT tool of the user. individual in such a way as to make believe that the person who impersonated has indeed entered his login credentials in a consenting manner. To make it simpler, a person can simply access your GMail account without even needing to enter the passwords and ID address.

We are still in the category of the most used techniques by hackers to attack the GMail account password. It falls into the category of what is commonly known as brute force attack or password cracking.
The dictionary attack is a variant that uses a set of connection data stored in a server called a dictionary. Thanks to an automated computer program, the hacker will try several times to find the password by trying all the possibilities he has stored in his dictionary. Since it is an automated script, the cracking is done much faster depending on the tool available to the hacker.

Malware plays a big role when hacking needs to be initiated. Concretely, it would be almost impossible to carry out a computer attack without the use of malware. But what malware are we talking about?
It should be mentioned that there are several. Malware is a computer program typically designed to violate the integrity of a computer system. The most popular used include:
Cyber threats are constantly evolving, making Gmail security more important than ever. Follow these practical steps to safeguard your account and personal information. Start by reviewing your Google Account Security Checkup to identify vulnerabilities.
Your Gmail account requires serious password protection. Here's how to do it right:
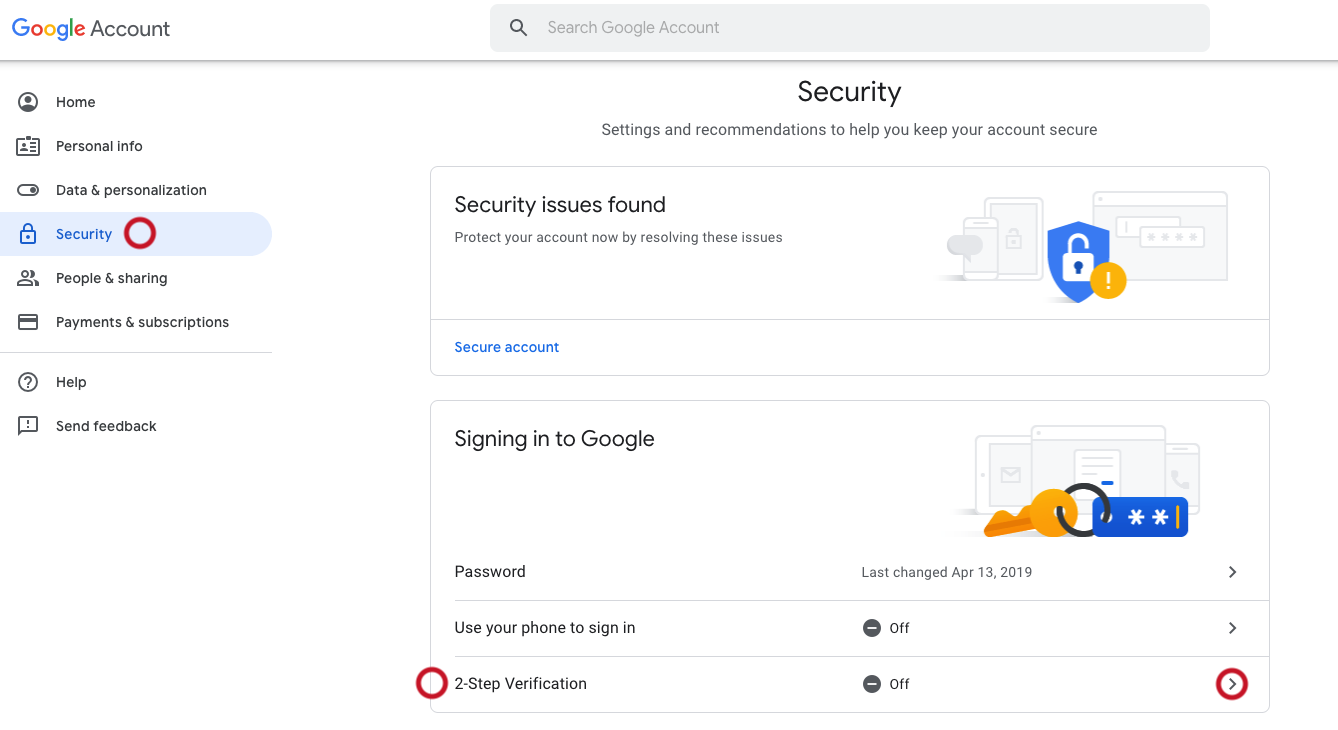
Add an extra layer of security to your Gmail account:
Outdated software creates security vulnerabilities. Protect yourself by:

Quality antivirus software is essential for Gmail security:
Many security breaches originate from suspicious extensions and apps. Take these steps:
Hackers often exploit weak security questions. Here's how to protect yourself:

Your device security directly impacts your Gmail account safety:
Even with precautions, no system is 100% secure. If you suspect unauthorized access:
Remember: Absolute cybersecurity doesn't exist, but following these steps significantly reduces your risk. Stay vigilant, keep your security settings updated, and act quickly if you notice suspicious activity on your Gmail account.
If you suspect that your GMail account has been hacked, it's important to take immediate action. First, try to regain control of your account by resetting your password. Ensure that you enable two-factor authentication for added security. Additionally, review your account settings and recent activity to identify any unauthorized changes or actions.
There are several steps you can take to enhance the security of your GMail account. These include using strong, unique passwords, enabling two-factor authentication, being cautious of phishing attempts, regularly updating your browser and security software, avoiding public WiFi networks for sensitive tasks and being mindful of the information you share online, especially in relation to secret questions and personal details.
No, hacking into someone's GMail account without their consent is illegal and constitutes a serious breach of privacy and security laws. Engaging in unauthorized access to another person's account can lead to severe legal consequences, including criminal charges and civil penalties.
If you believe that your GMail account has been compromised, immediately change your password and enable two-factor authentication if you haven't already done so. Review your account settings for any suspicious changes and consider notifying GMail support for further assistance. It's also advisable to scan your device for malware and to update your security software regularly.