Hack WiFi passwords
Here you will find a lot of tips hack WiFi passwords

Hack WiFi passwords
Here you will find a lot of tips hack WiFi passwords

The owners of WiFi routers or access points can allow free access to their WiFi without a code or any protection, but for what purpose? Out of kindness? It's possible, but also to be able to hack all your content and spy on you!
Once a computer or smartphone is connected to a network, it is visible to all other connected devices. It is important to have a good firewall so that no unwanted person can enter their private space. But that's not all, if a network is private and therefore secured with an access code, it is possible to break this lock.
Hackers use techniques to hack a WiFi code. They use packet analyzer that will simulate a connection and then try a whole bunch of possible and unimaginable combinations. The 3 minutes to crack WiFi. Useful when they need emergency internet access to send an email.
How do you proceed when you want to access WiFi that is protected by a password that you don't have? Do you perhaps use any tricks that we have already mentioned above?
If you're not a hacking expert, we have something that might interest you. Indeed, WiFi passwords are usually long and hard to remember—and you're never fully protected from a potential cyberattack that could allow a hacker to block your access to your hotspot.
PASS WIFI is a software program designed for anyone to use. With this tool, you don’t need to be a computer expert—even beginners can operate it effortlessly.
PASS WIFI hacks access to any WiFi network, regardless of its security level, thanks to its powerful algorithms. It easily retrieves any WiFi password from network databases, allowing you to connect to the internet from anywhere.
Using it is simple—just follow these three easy steps:
Moreover, when you download PASS WIFI for the first time, you get a 30-day free trial. At the end of this trial period, you’ll receive a full refund if it doesn't work. So there’s no reason to hesitate.
Try it now and say goodbye to connection hassles
What is dangerous is that if someone has access to your Internet connection, you are the one responsible for it. The law is very clear on it, the disorders are your responsibility. If the hacker does illegal things like downloading movies, music or worse, communicates with terrorists, you will be responsible for it. The police will trace your connection IP address and it will be up to you to prove your willingness to cooperate with justice by demonstrating that you have nothing to do with it. To do this, on your computer, go to the "Network" tab then look at the list of connected devices. If there are devices connected to it without being prompted, you can revoke them with their MAC address.
In addition, let's take a tour of the alternative techniques used by cybercriminals to hack a WiFi network:

Keylogger is usually classic when someone aims to hack into a WiFi network.
It should be noted simply that the keylogger falls under the category of spyware. It is therefore a malicious program whose use is prohibited by law. Its operation obviously depends on its installation on a computer device of the target.
Quite simply by detours. If the hacker is someone who is close to you, he may attempt to install them manually by grabbing your computer terminal. Let's say this is the easiest method. But if it's someone from afar, he will definitely try to push you to install it yourself. Either by convincing you to install it for any reason. Or, by trapping your connection with phishing methods.
As its name suggests, the keylogger is a computer program that finally gives its user the possibility of knowing everything that is typed on the keyboard of an infected terminal. In other words, if you are contaminated by this kind of programs, it will be easy for the hacker to recover your login credentials and hack your WiFi. The only way to circumvent hacking by a Keylogger is to use a virtual keyboard. Indeed, your mouse will be your keyboard, no physical key will be pressed so no hacking will be done.
In the context of WiFi, the man-in-the-middle attack stands out as one of the most effective methods.
In the man-in-the-middle attack, the objective of the cybercriminals is to create a barrage which will take the form of the user's targeted platform. In other words, this consists of pretending to be the computer server or the computer terminal with which the user wants to communicate. But it's not enough to impersonate this terminal. The idea is to act as a bridge. Clearly, the criminal will be the intermediary between the WiFi network of his target and the target itself.
This is very easy to guess, if the user believes he is connecting to his own WiFi Hotspot, he will try to authenticate his connection. For this he must enter the password. However, by doing this it is the cybercriminal who receives all this information. Data that can be used for a hacking project to the detriment of the user.
There are several ways to recover the password of a WiFi network to connect without even going through the WiFi owner. The method will vary depending on the type of device whether it is a computer or a smartphone.
For a computer running Windows, here is the procedure you need to follow:
For computers running Mac OS, here is the procedure to follow:
As for Android devices, the technique is much simpler:
Go to " settings ", then " connection ". Then click WiFi. You will see just at the top right a QR code. Click on the QR code and scan it. It will allow you to connect to WiFi without even needing the password.

We return to the category of malicious software like the previously mentioned Keylogger. Unlike the keylogger, the Trojan can be much easier to install on a target device. Indeed, it has the ability to hide behind a legitimate application that can be downloaded either from the Google Play Store or even from the Appstore. It may even be basically a legit application that hides its malicious functionality. The Trojan horse can then be used as classic spyware. That is, the hacker can exfiltrate your login data. And it can go far beyond simply stealing login data. It can also infect all WiFi as a whole and monitor all your traffic and that of the people who will use the Internet of this same Hotspot.

We return to a much more simplistic category which does not necessarily call for a very good mastery of hacking.
If social engineering is a technique that has been around for a very long time, it must be said that it is since last year that the practice has seen a very significant increase in its popularity. Especially with the Twitter hack. Social engineering is therefore this method which essentially draws its source from social relations, hence its name. In other words, the hacker who is behind the social engineering will first aim to make friends with you. When you are close enough, he will now seek to look at information of a somewhat personal or technical nature. Thanks to this information that he will have collected,. Consequently, one has the impression of being much more involved in manipulation than in actual computer hacking. However, it is clear that this technique really works and has already proven itself.

We are talking here about a technique that will be used a lot against WiFi Hotspots. Some hackers do not have time to do a lot of procedure in order to hack the password of a WiFi. So how do they do it? It is very simple. It uses software sophisticated enough to compose thousands or even millions of possible password combinations. The objective is to be able to find the password through random combinations. It can take 2 seconds, days, months, years depending on the difficulty of the password. There is the much more organized and less random variant which is the dictionary attack. The common points between the dictionary attack and the classic password cracking reside in the fact thatfind the right password. The difference is essentially that the dictionary attack relies on a set of passwords or combinations collected and stored in a " dictionary ". In other words, here the hacker does not create new combinations, he only tries combinations that already exist. He harvested them in different ways. Either using scrapping or taking advantage of data leaks to harvest loose databases. Which of course is not uncommon in the industry.
If you are the one using a Hotspot and need to improve your security, here are some tips that might help you stay safe:
A WiFi that is easily detectable by everyone can be targeted and very easily moreover… Because who would think of hacking a WiFi that he does not even see or of which he is unaware of the existence. Obviously, one of the disadvantages of this alternative will be to enter the name of the WiFi manually to allow connection. There is one thing that is quite particular, which the need for security can explain and justify that you accept these different concessions. And then being already connected to WiFi you will simply have to save the connection so as not to bother too much.
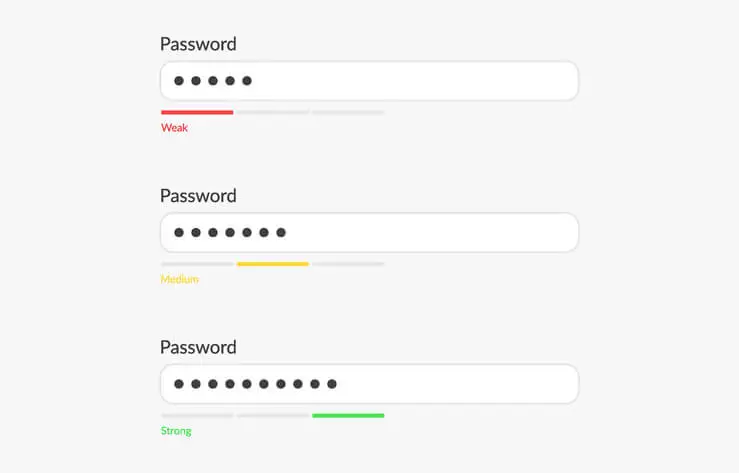
The password is the key to the security of your WiFi if it is badly constituted, it is obvious that you will be easily hacked. Therefore you should know that keeping your Hotspot's default password is the worst mistake possible. Cybercriminals are usually on the lookout for this kind of negligence. First please change your password. Then do not think of using your personal information for the composition of this same password. Follow the rules of good practice in terms of creating a password. Finally, if you want to keep your Hotspot secret and safe, don't write the password on bits of paper that can be lying around anywhere.
As for the composition of the password, it must be excluded dates of birth, birthdays or even telephone or bank account numbers. Cybercriminals already know the trick! Also, don't use the name of a loved one or your child. Disregard your privacy because it's the first thing cybercriminals will look for to hack you.

Whether it's a computer or a smartphone, you have to think regularly about its protection and security. Because vulnerability can come from where you least expect it. To avoid being exposed to the malware that we mentioned above, namely the keylogger or the Trojan horse, you must avoid downloading any application. You should also not use applications that come from application stores other than the most official, namely the Apple App store and the Google Play Store. Also, you should favor the use of antivirus software to increase the security of your device. Because we cannot know exactly when we are infected or not. Have a protection program that can ensure this and in addition not to be neglected. What's more, it is important to run its updates. Updates will allow you to close security vulnerabilities that are discovered either by your terminal manufacturer or by a software publisher that you commonly use. Don't be careless with its updates and take care to perform them on time and without delay. Finally, the security of your computer device is not complete if everyone can access it as they want. Indeed, you must ensure that access to your smartphone or computer is locked. For what reason do you think? Knowing that we tend to log our connection to our WiFi, it is not uncommon for traces of these connections to remain in our device. As we mentioned above, being able to easily access your terminal gives the advantage to anyone who wants to hack your WiFi. Therefore lock access to them. Use a password or biometric security method.

There are several methods used by cybercriminals to trick you into infecting your endpoints. They can also go through links. Therefore, when you receive a message with a link that invites you to perform an activity when you have not engaged anything, simply avoid clicking on this link. If you really want to check what's behind the link, try accessing it directly from your browser.

It is important that you change the password that allows you to connect to your WiFi Hotspot with some certainty. This is explained by a very obvious reality: Data Leaks. We are not immune to data leaks. Especially when the majority of those leaks are beyond our control. Leaks can expose our personal information without us even knowing it. It is in this context that hackers can use it and hack you. So the best method is to change the password regularly to protect yourself since the old one is already compromised.
Hacking into WiFi networks without authorization is illegal and punishable by law in most countries. It violates privacy and security laws.
Yes, PASS WIFI is designed to be user-friendly and can be used by anyone, regardless of their expertise in hacking. Even beginners can utilize it effectively.
PASS WIFI uses powerful algorithms to decrypt WiFi network passwords automatically. Users need to download and install the software, conduct a WiFi network search and select the network they want to connect to. PASS WIFI then provides the password within minutes.
Yes, PASS WIFI offers a 30-day trial period for users to test the software. Users can request a refund.
If someone gains unauthorized access to your Internet connection, you could be held responsible for any illegal activities conducted through it. It's essential to safeguard your connection to avoid legal consequences.
To enhance WiFi security, consider reducing the visibility of your WiFi network, creating strong passwords, regularly changing passwords, avoiding suspicious links and protecting your devices with security software.