How to hack a X password?
Learn how to hack X accounts

How to hack a X password?
Learn how to hack X accounts

Most of the time it is about reprisals by groups of political opponents in disagreement with the imposed regime. Indeed, most leaders have X accounts to communicate on the Internet but it is also the best way to crack passwords.
It is not interesting for hackers to hack a X password unless it is to harm the account holder. Which makes sense since everything posted is public. It is difficult to take possession of an account and then contact its list of friends in order to extract money as with other social network accounts. The only interest of the hackers is therefore to mark opposition messages or else to close the account.
Their techniques are very complex but some have been doing it since they were very young. From a laptop, they will launch thousands of requests per second to try to break security. It's the same principle as a padlock that you would like to break, with the only difference that this time everything is virtual.
Despite the fact that there is double authentication, a X account will never be well protected. For example, an airline account was cracked posting a naked woman on its page.
A hacker will also want to hack a X account to get revenge on someone, his girlfriend for example. To avoid this, the best is still to use a very long password. A sentence with one or two special characters is more effective than a whole bunch of weird characters. Indeed, computers nowadays are powerful enough to crack passwords in just a few minutes thanks to their embedded dictionary algorithm.
In summary we are going to write you some methods that could be used by cybercriminals to hack into your X account:
account
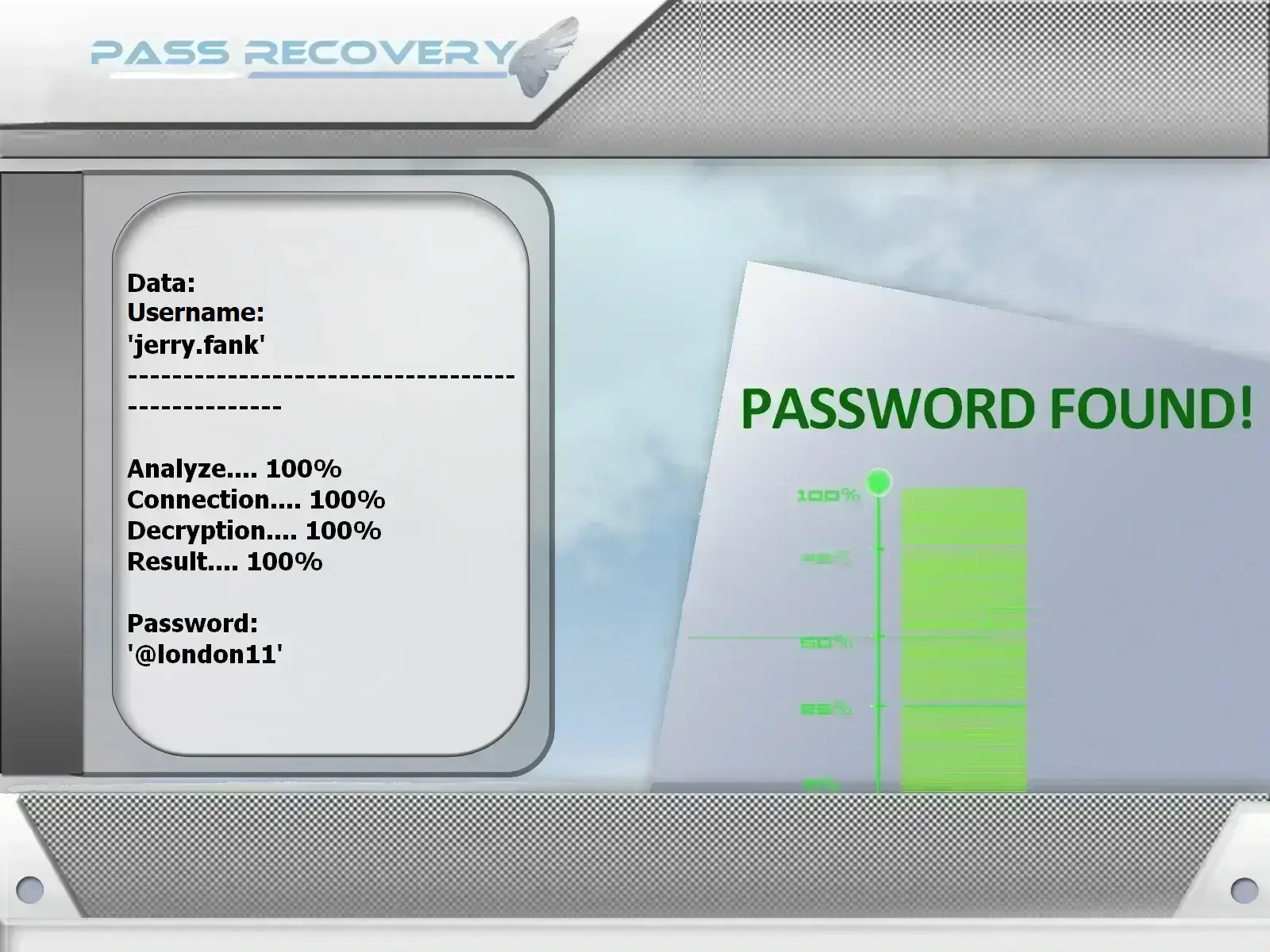
using PASS
RECOVERY
(also works with a phone number or @username).
Given that cybercriminals are always one step ahead, you need a reliable way to recover your X account. There are publicly available tools that make it easy to regain access to X accounts�PASS RECOVERY is a prime example. With it, you can recover your account in just a few minutes. You don�t need to worry about anything�it was specifically designed for anyone to use, even if you have no programming or technical expertise.
This is the simplest password recovery method available today. The only and best solution capable of accessing any X account! It effortlessly retrieves the password for any account with no usage limits!
Download PASS RECOVERY from its official website: https://www.passwordrevelator.net/en/passrecovery

Social engineering or social engineeringis not in the proper sense of the term piracy. In truth, it is a manipulation tactic that will consist of taking advantage of a friendly and emotional bond. The goal of social engineering is going to be to collect login data that can be converted and hack a target. We will talk about this one first because this method has already been used for successful hacks of several X accounts and it even made headlines. In this context, it is strongly recommended that users of social networks do not disclose too much personal information about themselves, especially when interacting with unknown people. It would also be necessary to avoid transferring the content of a message to a third party under the pretext of doing him a favor, never forward this message.

We continue in the category of the most popular hacking techniques. Through social networks such as X, phishing messages are very regular. So don't be surprised if you receive a message in private or on a tweet inviting you to click on a potential link. The trap is too beautiful. The advice remains the same, never click on a link you receive by message or in a questionable publication. In the Spearphishing variant which remains the most dangerous, the hacker will target his victim in a particular way. By collecting data on the latter, he will quite simply make him believe in the identity of the person who sends him the message. Therefore you must do everything to be as vigilant as possible. When you absolutely want to know what is hidden behind a link, it is strongly recommended to go directly to your browser and enter the address of the website concerned.

Hacking the SIM card is a method that is not well known but also has serious dangers. We certainly do not know it, but the SIM card is a computer tool that can be hacked. This is much more obvious when it comes to the e-SIM card. Simjacking gained momentum a few years ago after hackers and several IT service players discovered that a large part of the SIM cards released since the 2000s were no longer receiving security updates. A situation that has created a lot of security holes that can be exploited even today. In other words, no longer be vulnerable to these kinds of cyberattacks. By exploiting these hidden vulnerabilities in our SIM cards, cybercriminals have ample opportunity to steal our data. And who says data theft says possibility of hacking your online accounts.

It is still a method that relies on the SIM card. Unlike the previous technique, this one is not really hacking. However, it remains quite useful to facilitate a hacking practice. Why is this technique very dangerous? Just know that SIM Swapping is a method hackers use to hijack phone numbers. By hijacking the phone number, we are referring to the fact that they can have control of our phone contact and do whatever they want with it. How do they proceed then? Simply by calling your telephone operator. After providing information to pretend to be you, which is very easy because you can find everything on social networks these days, he will ask that your phone number be transferred to another chip.
And this is totally possible. When the hacker will have the new chip with your phone number, we let you guess the possibilities available to him. Taking into account the fact that the majority of our social network accounts are linked to this telephone number, the latter has the possibility of usurping control of its accounts and even changing the login credentials. A very effective technique that does not necessarily require very great hacking skills.
For those who have hacking skills at very high levels, this technique is definitely for them. It mainly concerns the hacking of cookies. Cookies are micro computer programs whose usefulness is to allow the recording of certain web traffic in order to facilitate a potential return from the user and to speed up the loading times of web pages. In other words, thanks to cookies, when you connect to a web platform that you have previously visited, it will be much easier for you to find your way and the time used will be reduced ostensibly. However, these small " computer cakes " are not just shortcuts. It is also a way to track users and sell them advertising. The problem behind cookies is that they can also be useful to hackers when crackers manage to steal them. This gives the advantage of being able to create another connection path that will allow them not only to hijack your traffic but also to be able to intercept them. In other words, this hacking technique is a way for hackers to collect data while letting you connect to the Internet as if nothing had happened. By monitoring you, they can then retrieve your login credentials and hack you later. This technique is also known as Session Hijacking or session hijacking.

The keylogger known as Keyloggers is a computer program that was designed to collect information but not just any information. As its name suggests, it is a computer tool whose basic functionality is the collection and transmission of any information typed on the keyboard of an infected computer device. In other words, if you get tricked by a keylogger, the hacker behind that program will grab whatever you type on your keyboard whether it's on a computer or a smartphone, giving him the advantage of having your login credentials. You then understand that your X account can easily be hijacked by this means. It is for this reason in particular that it is strongly recommended that you have an excellent antivirus or protection program on your device.

Data Leaks are a scourge of the Internet and the worst thing is that the user has no real way to protect himself directly against this problem. A data breach typically occurs when a platform that generates and collects user data loses control and exposes it to people who normally don't have the right to access it. Data leaks can be caused by hacking, by errors or negligence in the way servers are managed, or simply by the desire of some people to cause harm. Of course, the consequences remain the same. Indeed who says data leak, says data exposure. In other words, anyone can access this information and use it as they see fit. Actors are constantly on the lookout for this kind of opportunity. Collecting information without really making any effort...that's what a Data Leak represents. Data leaks are very common. There are even some that are not even published, so the general public does not know anything about it. In this context, you are exposed to cyber-maliciousness. Protect yourself by changing your passwords often.

It is clear that you need to be wary of threats much more often than you believe to be far from you. For example we can talk about spyware. Spyware is a computer program that is designed to monitor a person. If the spyware was previously used in professional or political cases, today there are consumer versions that all users can buy in computer stores such as the Dark Web and use them. Which means that you no longer need to be a hacking specialist to spy on you. Spyware can be used to monitor your traffic and harvest your personal data such as your login ID. If you are infected, the possibility of being hacked is clearly multiplied by 10. The advice remains the same for combating malware.

It's a kind of brute force attack. However, it is organized around a database called the dictionary. The dictionary attack will consist for the hacker to try thousands of combinations in order to find the right password, thanks to an automated computer program. These millions of combinations are actually already made up passwords that have been collected by various means. For example through phishing, data leaks or simply through social engineering. This technique is one of the most used to hijack your accounts. The only way you can protect yourself against the dictionary attack is to get into the habit of changing your passwords and not forming that login ID with your nominal information.

DNS attack is not very common. However, it can be very effective for hackers who know how to do it perfectly. DNS are web platforms that allow communication between the user and a website. Because of their important role in this ongoing communication, cybercriminals have found a way to hijack DNS functionality to use against users like us. In one variant of DNS Spoofing known as DNS poisoning, attackers use DNS caches and poison them with malicious codes. When they do, it gives them the opportunity to hijack someone's connection even if they type in an address from their browser.

We are all WiFi users these days. What we particularly like is most certainly using free WiFi where access is not password protected. This is especially possible when we are in restaurants, waiting rooms even in a workplace. The problem with connections to free WiFi networks is the difficulty of knowing if the Hotspot we are using is secure or not. The importance of determining this lies in the fact that the Accords have found a method to hack us. And WiFi hotspots are particularly useful in their new strategy. How does he proceed?
They manage to do this by creating a fake Wireless Hotspot. Most often the fake Hotspot impersonates another which is commonly used by the targets. The moment they connect, their internet traffic is intercepted by this which can easily collect their personal and login data.
To protect yourself and ensure that your account is not usurped, you must adopt the best practices in terms of digital protection. In a certain way you will reduce the risks and protect yourself from computer crackers.
Among other things, it is very important that you have a good foundation. For it:
Attempting to hack someone's X password is illegal and unethical. It violates privacy and can have serious legal consequences.
To protect your X account, ensure you have a strong, unique password, enable two-factor authentication, be cautious of phishing attempts and avoid sharing personal information online.
Yes, if your X account is hacked, you can attempt to recover it by following the account recovery process provided by X. This may involve resetting your password and verifying your identity.
If you suspect your X account has been compromised, immediately change your password, revoke access to any third-party applications and report the issue to X's support team.
Accessing someone's X account without their consent is illegal. If you require access to an account for legitimate reasons, such as law enforcement investigations, it is essential to obtain proper authorization and follow legal procedures.
To enhance the security of your online accounts, use strong, unique passwords for each account, enable two-factor authentication whenever possible, regularly update your passwords and stay vigilant against phishing attempts.